Slide 1
... random bits of data known as a keystream. These pseudorandom bits are equal in length to the plaintext data that is to be encrypted. The pseudorandom bits in the keystream are then combined with the plaintext data bits by using a Boolean XOR process. The end result is the WEP ciphertext, which is th ...
... random bits of data known as a keystream. These pseudorandom bits are equal in length to the plaintext data that is to be encrypted. The pseudorandom bits in the keystream are then combined with the plaintext data bits by using a Boolean XOR process. The end result is the WEP ciphertext, which is th ...
Accounts and Authentication
... Distributing system configuration data such as user and host names between computers on a computer network. Used for maintenance and distribution of a central directory of user and group information, hostnames, email aliases and other text-based tables of information in a computer network. NIS ...
... Distributing system configuration data such as user and host names between computers on a computer network. Used for maintenance and distribution of a central directory of user and group information, hostnames, email aliases and other text-based tables of information in a computer network. NIS ...
Term
... Layer to counter the issues related to wired equivalent privacy (WEP). The existing 802.11 standard specifies the use of relatively weak, static encryption keys without any form of key distribution management. This makes it possible for hackers to access and decipher WEPencrypted data on your WLAN. ...
... Layer to counter the issues related to wired equivalent privacy (WEP). The existing 802.11 standard specifies the use of relatively weak, static encryption keys without any form of key distribution management. This makes it possible for hackers to access and decipher WEPencrypted data on your WLAN. ...
Edge Port Security using IEEE 802.1x
... Most switch vendors enhance this with multi-method and multi-user authentication ...
... Most switch vendors enhance this with multi-method and multi-user authentication ...
Giuseppe Razzano , Neeli R. Prasad , Roberto De Paolis
... 802.11i is the new version of the standard, finalized in 2004 by IEEE Taskgroup i, with the aim of solving the weaknesses of WEP-based wireless security. Substantial components of the 802.11i standard were already released before the standard was released and products are available on the market, un ...
... 802.11i is the new version of the standard, finalized in 2004 by IEEE Taskgroup i, with the aim of solving the weaknesses of WEP-based wireless security. Substantial components of the 802.11i standard were already released before the standard was released and products are available on the market, un ...
802.1X
... EAP methods can have different goals, and therefore, often use many different methods for authenticating users depending on the requirements of a particular situation ...
... EAP methods can have different goals, and therefore, often use many different methods for authenticating users depending on the requirements of a particular situation ...
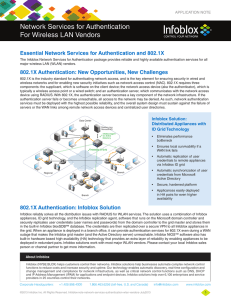
Network Services for Authentication For Wireless LAN
... in the built-in Infoblox bloxSDB™ database. The credentials are then replicated over a secure VPN to all Infoblox appliances in the grid. When an appliance is deployed in a branch office, it can provide authentication services for 802.1X even during a WAN outage that makes the Infoblox grid master ( ...
... in the built-in Infoblox bloxSDB™ database. The credentials are then replicated over a secure VPN to all Infoblox appliances in the grid. When an appliance is deployed in a branch office, it can provide authentication services for 802.1X even during a WAN outage that makes the Infoblox grid master ( ...
Chapter 21 PowerPoint Presentation
... • A RADIUS server validates the RADIUS client request. • Windows 2000 uses Internet Authentication Services (IAS) to perform authentication. ...
... • A RADIUS server validates the RADIUS client request. • Windows 2000 uses Internet Authentication Services (IAS) to perform authentication. ...
New 802.11 Security Standards
... encryption to and from 802.1X EAP server – Key in a pass phrase (master key) in both client and AP – If pass phrase matches, then AP allows entry to the ...
... encryption to and from 802.1X EAP server – Key in a pass phrase (master key) in both client and AP – If pass phrase matches, then AP allows entry to the ...
802.11 Security/Bluetooth
... • Host/AP share 40 bit symmetric key (semi-permanent) • Host appends 24-bit initialization vector (IV) to create 64-bit key • 64 bit key used to generate stream of keys, kiIV • kiIV used to encrypt ith byte, di, in frame: ...
... • Host/AP share 40 bit symmetric key (semi-permanent) • Host appends 24-bit initialization vector (IV) to create 64-bit key • 64 bit key used to generate stream of keys, kiIV • kiIV used to encrypt ith byte, di, in frame: ...