22C:19 Discrete Math
... A linear congruence is of the form ax ≡ b (mod m) Where a, b, m are integers, and x is a variable. To solve it, find all integers that satisfies this congruence What is the solution of 3x ≡ 4 (mod 7)? First, we learn about the inverse. ...
... A linear congruence is of the form ax ≡ b (mod m) Where a, b, m are integers, and x is a variable. To solve it, find all integers that satisfies this congruence What is the solution of 3x ≡ 4 (mod 7)? First, we learn about the inverse. ...
CHAPTER 01 - Basics of coding theory
... by Bob: Alice chooses p and an elliptic curve E (mod p), a point P on E and calculates the number of points n on E (mod p) – what can be done, and we assume that 0 < m < n. Alice then chooses a secret a and computes Q = aP. Alice makes public p, E, P, Q and keeps secret a. To sign m Alice does the f ...
... by Bob: Alice chooses p and an elliptic curve E (mod p), a point P on E and calculates the number of points n on E (mod p) – what can be done, and we assume that 0 < m < n. Alice then chooses a secret a and computes Q = aP. Alice makes public p, E, P, Q and keeps secret a. To sign m Alice does the f ...
Postscript (PS)
... called the "ternary" Goldbach conjecture), written in a June 7, 1742 letter to Euler, states that every integer is the sum of three primes [1]. As re-expressed by Euler, an equivalent of this conjecture (called the "strong" or "binary" Goldbach conjecture) asserts that all positive even can be expre ...
... called the "ternary" Goldbach conjecture), written in a June 7, 1742 letter to Euler, states that every integer is the sum of three primes [1]. As re-expressed by Euler, an equivalent of this conjecture (called the "strong" or "binary" Goldbach conjecture) asserts that all positive even can be expre ...
Linear Algebra Review
... computers. The most common way for text to be stored on computers is through the American Standard Code for Information Interchange, or ASCII for short. The ASCII table for the computer keyboard characters is given as follows. ...
... computers. The most common way for text to be stored on computers is through the American Standard Code for Information Interchange, or ASCII for short. The ASCII table for the computer keyboard characters is given as follows. ...
Lecture 6: RSA
... Using an ordinary cryptosystem, encryption uses a key K and decryption is performed by reversing each step of the encryption and hence it uses the same key K. Could there be another way where you could use one key, E, to encrypt and another key, D, to decrypt the message? In this case decryption can ...
... Using an ordinary cryptosystem, encryption uses a key K and decryption is performed by reversing each step of the encryption and hence it uses the same key K. Could there be another way where you could use one key, E, to encrypt and another key, D, to decrypt the message? In this case decryption can ...
Pseudorandom_number_generation_QiuliangTang_revision
... ki = G(t, s) mod q s = (1 + s + ki) mod 2b Return (k1, k2, …, km) m pseudo-random numbers in [0, q-1] ...
... ki = G(t, s) mod q s = (1 + s + ki) mod 2b Return (k1, k2, …, km) m pseudo-random numbers in [0, q-1] ...
a+b
... Provide descriptions and analysis Provide three implementations in two languages (reference and optimized in C,optimized in Java) IF selected, royalty free world wide ...
... Provide descriptions and analysis Provide three implementations in two languages (reference and optimized in C,optimized in Java) IF selected, royalty free world wide ...
Public-key cryptography and message authentication
... discrete logarithms (similar to factoring) – hard ...
... discrete logarithms (similar to factoring) – hard ...
Algorithms for Public Key Cryptography Computing Square Roots
... Thus, all the ui’s do not satisfy the equation. Since they are all distinct, for any number wi which satisfy the equation, there is at least one other number which do not satisfy the equation. Thus, the probability that a random a do not satisfy the equation is at least half. ...
... Thus, all the ui’s do not satisfy the equation. Since they are all distinct, for any number wi which satisfy the equation, there is at least one other number which do not satisfy the equation. Thus, the probability that a random a do not satisfy the equation is at least half. ...
VI-I Computing Euler`s function
... RSA problem is hard to solve when the modulous n is sufficiently large and randomly generated. The RSA problem is the main or the basis for the security of RSA public key encryption and RSA digital signature schemes. RSA problem for very small exponents would be easier than integer factoring. All th ...
... RSA problem is hard to solve when the modulous n is sufficiently large and randomly generated. The RSA problem is the main or the basis for the security of RSA public key encryption and RSA digital signature schemes. RSA problem for very small exponents would be easier than integer factoring. All th ...
MTH2125: Discrete Mathematics Tutorial Questions II Dr. John O
... A parking lot has 31 visitor spaces, numbered from 0 to 30. Visitors are assigned parking spaces using the hashing function: h(k) = k mod m, where k is the number formed from the first three digits on a visitor’s license plates, and m is the number of available parking spaces. Which spaces are assig ...
... A parking lot has 31 visitor spaces, numbered from 0 to 30. Visitors are assigned parking spaces using the hashing function: h(k) = k mod m, where k is the number formed from the first three digits on a visitor’s license plates, and m is the number of available parking spaces. Which spaces are assig ...
MTH2125: Discrete Mathematics Tutorial Questions 3 Dr. John O
... A parking lot has 31 visitor spaces, numbered from 0 to 30. Visitors are assigned parking spaces using the hashing function: h(k) = k mod m, where k is the number formed from the first three digits on a visitor’s license plates, and m is the number of available parking spaces. Which spaces are assig ...
... A parking lot has 31 visitor spaces, numbered from 0 to 30. Visitors are assigned parking spaces using the hashing function: h(k) = k mod m, where k is the number formed from the first three digits on a visitor’s license plates, and m is the number of available parking spaces. Which spaces are assig ...
Efficient signature generation by smart cards
... Journal of Cryptology 9 1991 International Association for Cryptologic Research ...
... Journal of Cryptology 9 1991 International Association for Cryptologic Research ...
The Fundamentals: Algorithms, the Integers, and Matrices
... Julius Caesar created secret messages by shifting each letter three letters forward in the alphabet (sending the last three letters to the first three letters.) For example, the letter B is replaced by E and the letter X is replaced by A. This process of making a message secret is an example of encr ...
... Julius Caesar created secret messages by shifting each letter three letters forward in the alphabet (sending the last three letters to the first three letters.) For example, the letter B is replaced by E and the letter X is replaced by A. This process of making a message secret is an example of encr ...
RSA - people.vcu.edu - Virginia Commonwealth University
... Needed for Security: 1. One of the two keys must be kept secret. 2. It must be impossible or at least impractical to decipher a message if no other information is available. 3. Knowledge of the algorithm plus one of the keys plus samples of ciphertext must be insufficient to determine the other key. ...
... Needed for Security: 1. One of the two keys must be kept secret. 2. It must be impossible or at least impractical to decipher a message if no other information is available. 3. Knowledge of the algorithm plus one of the keys plus samples of ciphertext must be insufficient to determine the other key. ...
Slide 1
... Basics of web-based IS (www, web2.0, …) Markup’s, HTML, XML Design tools for Info Sys: UML ...
... Basics of web-based IS (www, web2.0, …) Markup’s, HTML, XML Design tools for Info Sys: UML ...
Lecture 13
... • Encryption methods, which are based on the “secret key” function have one, but significant disadvantage: it is necessary to distribute a key among all users and all of them must take care of keeping the key unavailable to others. • The alternative is an “open key” encryption, which became very pop ...
... • Encryption methods, which are based on the “secret key” function have one, but significant disadvantage: it is necessary to distribute a key among all users and all of them must take care of keeping the key unavailable to others. • The alternative is an “open key” encryption, which became very pop ...
Number Theory: Applications
... Representation of Integers I Number Theory: Applications CSE235 Introduction Hash Functions Pseudorandom Numbers Representation of Integers Integer Operations Modular Exponentiation ...
... Representation of Integers I Number Theory: Applications CSE235 Introduction Hash Functions Pseudorandom Numbers Representation of Integers Integer Operations Modular Exponentiation ...
CHAPTER FIVE
... In the real world , key management is the hardest part of cryptology .Cryptanalysts often attack cipher system through their key management .One of the problems facing symmetric cipher systems is key distribution Keys must be distributed in secret , since knowledge of the key gives knowledge of the ...
... In the real world , key management is the hardest part of cryptology .Cryptanalysts often attack cipher system through their key management .One of the problems facing symmetric cipher systems is key distribution Keys must be distributed in secret , since knowledge of the key gives knowledge of the ...
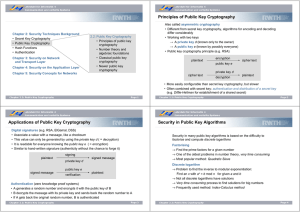
Principles of Public Key Cryptography Applications of
... • Choose e as relatively prime to (p - 1) · (q - 1) a.) by choosing e at random and test if it is relatively prime to (p - 1) · (q - 1) b.) by choosing e first and then determine matching p and q → RSA is not less secure if always the same e is chosen → If e is small or its binary representation has ...
... • Choose e as relatively prime to (p - 1) · (q - 1) a.) by choosing e at random and test if it is relatively prime to (p - 1) · (q - 1) b.) by choosing e first and then determine matching p and q → RSA is not less secure if always the same e is chosen → If e is small or its binary representation has ...
Data Encryption and Decryption Using New Pythagorean Triple
... ISSN: 2078-0958 (Print); ISSN: 2078-0966 (Online) ...
... ISSN: 2078-0958 (Print); ISSN: 2078-0966 (Online) ...
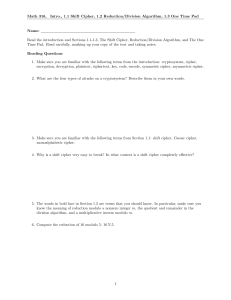
Reading questions for each topic
... Read the introduction and Sections 1.1-1.3, The Shift Cipher, Reduction/Division Algorithm, and The One Time Pad. Read carefully, marking up your copy of the text and taking notes. Reading Questions 1. Make sure you are familiar with the following terms from the introduction: cryptosystem, cipher, e ...
... Read the introduction and Sections 1.1-1.3, The Shift Cipher, Reduction/Division Algorithm, and The One Time Pad. Read carefully, marking up your copy of the text and taking notes. Reading Questions 1. Make sure you are familiar with the following terms from the introduction: cryptosystem, cipher, e ...
Public Key Cryptography and RSA Review: Number Theory Basics
... – square & multiply algorithm – RSA implementation ...
... – square & multiply algorithm – RSA implementation ...
Still Image Compression
... element in this group? RSA stands for Robust Security Algorithm, right? If e is small (such as 3) ...
... element in this group? RSA stands for Robust Security Algorithm, right? If e is small (such as 3) ...