Computer Architectures
... fashion, with instructions coming in one side and results out the other. Due to the reduced complexity of the Classic RISC pipeline, the pipelined core and an instruction cache could be placed on the same size die that would otherwise fit the core alone on a CISC design. This was the real reason tha ...
... fashion, with instructions coming in one side and results out the other. Due to the reduced complexity of the Classic RISC pipeline, the pipelined core and an instruction cache could be placed on the same size die that would otherwise fit the core alone on a CISC design. This was the real reason tha ...
20000525 052 THESIS . I
... access controls depending on the type of policy being enforced. In a computer system with discretionary access controls, selected users decide who can access the data and can specify the mode of access allowed. There are several mechanisms implemented on the computer systems for controlling discreti ...
... access controls depending on the type of policy being enforced. In a computer system with discretionary access controls, selected users decide who can access the data and can specify the mode of access allowed. There are several mechanisms implemented on the computer systems for controlling discreti ...
The Analytical Engine
... different institutions with (proposed) sites in separate regions, but if everything now planned comes to fruition, they should complement each other to make the Bay Area a world center and destination for computer history. Okay. Kudos. Deep sigh. Our painful concern of three and four years ago, that ...
... different institutions with (proposed) sites in separate regions, but if everything now planned comes to fruition, they should complement each other to make the Bay Area a world center and destination for computer history. Okay. Kudos. Deep sigh. Our painful concern of three and four years ago, that ...
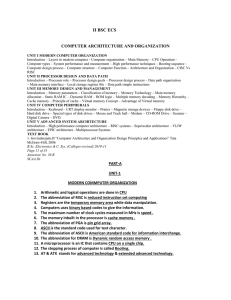
CAO - E
... are severely limited, but they are practical for certain functions such as phone books and calendars. Palmtops that use a pen rather than a keyboard for input are often called hand-held computers or PDAs. Because of their small size, most palmtop computers do not include disk drives. However, many c ...
... are severely limited, but they are practical for certain functions such as phone books and calendars. Palmtops that use a pen rather than a keyboard for input are often called hand-held computers or PDAs. Because of their small size, most palmtop computers do not include disk drives. However, many c ...
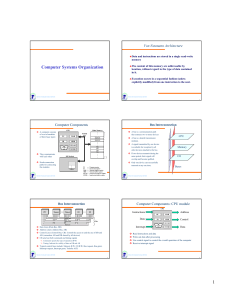
Computer Systems Organization
... (the term programming here means writing values into a ROM). These devices are denser and cheaper to manufacture than other type of ROM. ...
... (the term programming here means writing values into a ROM). These devices are denser and cheaper to manufacture than other type of ROM. ...
Computer Organization And Architecture Srm
... •Main memory is the second major subsystem in a computer. It consists of a collection of storage locations, each with a unique identifier, called an address. •Data is transferred to and from memory in groups of bits called words. A word can be a group of 8 bits, 16 bits, 32 bits or 64 bits (and grow ...
... •Main memory is the second major subsystem in a computer. It consists of a collection of storage locations, each with a unique identifier, called an address. •Data is transferred to and from memory in groups of bits called words. A word can be a group of 8 bits, 16 bits, 32 bits or 64 bits (and grow ...
UNIT-I - CSE Department B
... •Main memory is the second major subsystem in a computer. It consists of a collection of storage locations, each with a unique identifier, called an address. •Data is transferred to and from memory in groups of bits called words. A word can be a group of 8 bits, 16 bits, 32 bits or 64 bits (and grow ...
... •Main memory is the second major subsystem in a computer. It consists of a collection of storage locations, each with a unique identifier, called an address. •Data is transferred to and from memory in groups of bits called words. A word can be a group of 8 bits, 16 bits, 32 bits or 64 bits (and grow ...
Chapter 2: Constants, variables and data types
... • the data and the program are both stored in the computer’s memory in the same place • all instructions and data will be stored in the same place as binary numbers. This means data and instructions are indistinguishable from each other in memory. ...
... • the data and the program are both stored in the computer’s memory in the same place • all instructions and data will be stored in the same place as binary numbers. This means data and instructions are indistinguishable from each other in memory. ...
Motorola 68000

The Motorola 68000 (""'sixty-eight-thousand'""; also called the m68k or Motorola 68k, ""sixty-eight-kay"") is a 16/32-bit CISC microprocessor core designed and marketed by Motorola Semiconductor Products Sector (now Freescale Semiconductor). Introduced in 1979 with HMOS technology as the first member of the successful 32-bit m68k family of microprocessors, it is generally software forward compatible with the rest of the line despite being limited to a 16-bit wide external bus. After 35 years in production, the 68000 architecture is still in use.