Random Early Detection Gateways for Congestion Avoidance
... full then the gateway drops each arriving packet with probability 0.02. Zhang [36] shows that this version of Early Random Drop gateways was not successful in controlling misbehaving users. In these simulations, with both Random Drop and Early Random Drop gateways, the misbehaving users received ro ...
... full then the gateway drops each arriving packet with probability 0.02. Zhang [36] shows that this version of Early Random Drop gateways was not successful in controlling misbehaving users. In these simulations, with both Random Drop and Early Random Drop gateways, the misbehaving users received ro ...
Supporting Differentiated Service Classes: Queue Scheduling
... applications for a number of classic queue scheduling disciplines to help you better understand the range of options that are available. The traditional queue scheduling disciplines that we’ll consider here include: ...
... applications for a number of classic queue scheduling disciplines to help you better understand the range of options that are available. The traditional queue scheduling disciplines that we’ll consider here include: ...
Rate Limiting
... QoS is a set of techniques to manage network resources, including delay, delay variation, bandwidth and packet loss. Users or data flows are able to be guaranteed a certain level of performance ...
... QoS is a set of techniques to manage network resources, including delay, delay variation, bandwidth and packet loss. Users or data flows are able to be guaranteed a certain level of performance ...
Cisco QoS Notes - The Cisco Learning Network
... Mechanisms) will take over and schedule packets as they arrive at the interface. The TxQ queue ALWAYS uses FIFO and cannot be configured to use anything else. If the TxQ queue is not congested, then any packets that arrive at the interface will bypass the software queuing process and be sent directl ...
... Mechanisms) will take over and schedule packets as they arrive at the interface. The TxQ queue ALWAYS uses FIFO and cannot be configured to use anything else. If the TxQ queue is not congested, then any packets that arrive at the interface will bypass the software queuing process and be sent directl ...
Chapter 7 Packet-Switching Networks
... Suppose the following network uses flooding as the routing algorithm. If a packet sent by A to D has a maximum hop of 3, list all the routes it will take. Also tell how many hops worth of bandwidth it consumes. Assume the bandwidth weight of the lines is the same. ...
... Suppose the following network uses flooding as the routing algorithm. If a packet sent by A to D has a maximum hop of 3, list all the routes it will take. Also tell how many hops worth of bandwidth it consumes. Assume the bandwidth weight of the lines is the same. ...
Flow Control
... First rate-based flow control scheme Separates error control (window) and flow control (no coupling) So, losses and retransmissions do not affect the flow rate Application data sent as a series of buffers, each at a particular rate Rate = (burst size + burst rate) so granularity of control = burst I ...
... First rate-based flow control scheme Separates error control (window) and flow control (no coupling) So, losses and retransmissions do not affect the flow rate Application data sent as a series of buffers, each at a particular rate Rate = (burst size + burst rate) so granularity of control = burst I ...
Lecture 8: Architecture and Algorithms for Providing Quality of Service
... The host injects one packet per clock tick onto the ...
... The host injects one packet per clock tick onto the ...
ECE544Lec7QoSDR06
... • Best-effort expected to make up bulk of traffic, but revenue from first class important to economic base (will pay for more plentiful bandwidth overall) • Not motivated by real-time! Motivated by economics and assurances ...
... • Best-effort expected to make up bulk of traffic, but revenue from first class important to economic base (will pay for more plentiful bandwidth overall) • Not motivated by real-time! Motivated by economics and assurances ...
CS 552 Computer Networks Quality Of Service
... – r – average rate – b – token depth Assume flow arrival rate <= R bps (e.g., R link capacity) A bit is transmitted only when there is an available token Arrival curve – maximum amount of bits transmitted by time t ...
... – r – average rate – b – token depth Assume flow arrival rate <= R bps (e.g., R link capacity) A bit is transmitted only when there is an available token Arrival curve – maximum amount of bits transmitted by time t ...
ppt
... Possible Token Bucket Uses • Shaping, policing, marking • Delay pkts from entering net (shaping) • Drop pkts that arrive without tokens (policing) • Let all pkts pass through, mark ones without tokens • Network drops pkts without tokens in time of congestion ...
... Possible Token Bucket Uses • Shaping, policing, marking • Delay pkts from entering net (shaping) • Drop pkts that arrive without tokens (policing) • Let all pkts pass through, mark ones without tokens • Network drops pkts without tokens in time of congestion ...
ppt
... Possible Token Bucket Uses • Shaping, policing, marking • Delay pkts from entering net (shaping) • Drop pkts that arrive without tokens (policing) • Let all pkts pass through, mark ones without tokens • Network drops pkts without tokens in time of congestion ...
... Possible Token Bucket Uses • Shaping, policing, marking • Delay pkts from entering net (shaping) • Drop pkts that arrive without tokens (policing) • Let all pkts pass through, mark ones without tokens • Network drops pkts without tokens in time of congestion ...
Document
... – the Leaky Bucket traffic shaper: » uses a buffer whose content is read out periodically at a constant rate - the bucket in this case is a buffer that stores packets ...
... – the Leaky Bucket traffic shaper: » uses a buffer whose content is read out periodically at a constant rate - the bucket in this case is a buffer that stores packets ...
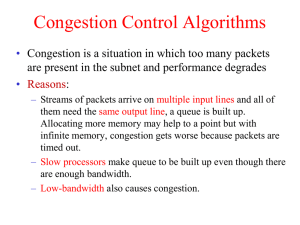
EECC694 - Shaaban
... – Used only when other congestion control methods in place fail. – When capacity is reached, routers or switches may discard a number of incoming packets to reduce their load. EECC694 - Shaaban #4 lec #8 Spring2000 3-30-2000 ...
... – Used only when other congestion control methods in place fail. – When capacity is reached, routers or switches may discard a number of incoming packets to reduce their load. EECC694 - Shaaban #4 lec #8 Spring2000 3-30-2000 ...
Powerpoint
... – explicit: send congestion info back to source – implicit: source deduced congestion (by looking at round-trip time for acks, say) ...
... – explicit: send congestion info back to source – implicit: source deduced congestion (by looking at round-trip time for acks, say) ...
Chapter 5
... Flows can be buffered on the receiving side before being delivered. Buffering does not affect the reliability or bandwidth, and increases the delay, but it smooths out the jitter. ...
... Flows can be buffered on the receiving side before being delivered. Buffering does not affect the reliability or bandwidth, and increases the delay, but it smooths out the jitter. ...
best-effort service!
... • Provides the abstraction of a “virtual pipe” between an ingress and an egress router • Network: – No loss – low delay & jitter ...
... • Provides the abstraction of a “virtual pipe” between an ingress and an egress router • Network: – No loss – low delay & jitter ...
15-744: Computer Networking
... and allow source to exceed profile • Based on expected capacity usage profiles • Traffic unlikely to be dropped if user maintains profile • Out-of-profile traffic marked ...
... and allow source to exceed profile • Based on expected capacity usage profiles • Traffic unlikely to be dropped if user maintains profile • Out-of-profile traffic marked ...
CS 456: Computer Networks: Congestion Control/QoS
... propagation delay is approx. 48 milliseconds Suppose a file transfer is initiated, congestion occurs, and implicit congestion control is used ...
... propagation delay is approx. 48 milliseconds Suppose a file transfer is initiated, congestion occurs, and implicit congestion control is used ...
r08-QoS - Computer Engineering
... • If conditions do not change, commit to current service • If conditions change, take steps to deliver consistent performance (help apps minimize playback delay) • Implicit assumption – network does not change much over time ...
... • If conditions do not change, commit to current service • If conditions change, take steps to deliver consistent performance (help apps minimize playback delay) • Implicit assumption – network does not change much over time ...
Network Layer (Congestion and QoS)
... A lighter approach to QoS IntServ is very powerful but has some severe drawbacks: - There is a setup phase, this cases delay in starting data flow. - Routers need to maintain per-flow state. This approach is flow-based and not very scalable. - Complex router-to-router exchange of flow information. ...
... A lighter approach to QoS IntServ is very powerful but has some severe drawbacks: - There is a setup phase, this cases delay in starting data flow. - Routers need to maintain per-flow state. This approach is flow-based and not very scalable. - Complex router-to-router exchange of flow information. ...
Network Layer 2 - Faruk Hadziomerovic
... Fragmentation when the elementary data size is 1 byte. (a) Original packet, containing 10 data bytes. (b) Fragments after passing through a network with maximum packet size of 8 payload bytes plus header. (c) Fragments after passing through a size 5 gateway. ...
... Fragmentation when the elementary data size is 1 byte. (a) Original packet, containing 10 data bytes. (b) Fragments after passing through a network with maximum packet size of 8 payload bytes plus header. (c) Fragments after passing through a size 5 gateway. ...
Leaky bucket
The leaky bucket is an algorithm used in packet switched computer networks and telecommunications networks. It can be used to check that data transmissions, in the form of packets, conform to defined limits on bandwidth and burstiness (a measure of the unevenness or variations in the traffic flow). It can also be used as a scheduling algorithm to determine the timing of transmissions that will comply with the limits set for the bandwidth and burstiness: see network scheduler. The leaky bucket algorithm is also used in leaky bucket counters, e.g. to detect when the average or peak rate of random or stochastic events or stochastic processes exceed defined limits.A version of the leaky bucket, the Generic Cell Rate Algorithm, is recommended for Asynchronous Transfer Mode (ATM) networks in Usage/Network Parameter Control at User–Network Interfaces or Inter-Network Interfaces or Network-Network Interfaces to protect a network from excessive traffic levels on connections routed through it. The Generic Cell Rate Algorithm, or an equivalent, may also be used to shape transmissions by a Network Interface Card onto an ATM network (i.e. on the user side of the User-Network Interface), e.g. to levels below the levels set for Usage/Network Parameter Control in the network to prevent it taking action to further limit that connection.