Chapter 5 - Department of Computer Science and Engineering, CUHK
... thin coaxial cable in a bus topology ...
... thin coaxial cable in a bus topology ...
AT16827: TCP/IP Server-Client with CycloneTCP
... networks will be interconnected using many routers. The request from clients has to pass through many networks to reach the destined server. The routers with routing tables helps in finding the right direction. The routers will not check the entire message to direct the data to next router which is ...
... networks will be interconnected using many routers. The request from clients has to pass through many networks to reach the destined server. The routers with routing tables helps in finding the right direction. The routers will not check the entire message to direct the data to next router which is ...
Document
... o Congestion: should avoid overloading some communication lines and routers o Quality of service: offer the appropriate service o Internetworking: deal with network differences, if source and destination are connected to different networks ...
... o Congestion: should avoid overloading some communication lines and routers o Quality of service: offer the appropriate service o Internetworking: deal with network differences, if source and destination are connected to different networks ...
Fitz and Dennis TB ch08 File
... a. process all messages, even if the messages are not explicitly addressed to them b. can translate one network protocol into another c. are less complex than bridges d. are most often used as the interface between two or more networks that have similar data link and network layer protocols e. canno ...
... a. process all messages, even if the messages are not explicitly addressed to them b. can translate one network protocol into another c. are less complex than bridges d. are most often used as the interface between two or more networks that have similar data link and network layer protocols e. canno ...
NETWORK TECHNOLOGIES AND APPLICATIONS
... 1. Physical Layer: This layer conveys the bit stream - electrical impulse, light or radio signal -- through the network at the electrical and mechanical level. It provides the hardware means of sending and receiving data on a carrier, including defining cables, cards and physical aspects. Fast Ether ...
... 1. Physical Layer: This layer conveys the bit stream - electrical impulse, light or radio signal -- through the network at the electrical and mechanical level. It provides the hardware means of sending and receiving data on a carrier, including defining cables, cards and physical aspects. Fast Ether ...
Lecture Note 6 - Computing Science
... encapsulate datagram into frame, adding header, trailer channel access if shared medium ‘physical addresses’ used in frame headers to identify source, dest • different from IP address! ...
... encapsulate datagram into frame, adding header, trailer channel access if shared medium ‘physical addresses’ used in frame headers to identify source, dest • different from IP address! ...
Deploying Very High Density Wi-‐Fi
... This document addresses factors and concerns related to very dense Wi-‐Fi environments such as stadiums. Because venues can differ radically, it is impossible to develop a single approach that adequately add ...
... This document addresses factors and concerns related to very dense Wi-‐Fi environments such as stadiums. Because venues can differ radically, it is impossible to develop a single approach that adequately add ...
The TCP/IP Protocol Suite
... The application layer is the topmost level of the TCP/IP protocol suite. It receives data from user applications and issues requests to the transport layer. The details of moving data between the application and other computers is shielded by the underlying layers. ...
... The application layer is the topmost level of the TCP/IP protocol suite. It receives data from user applications and issues requests to the transport layer. The details of moving data between the application and other computers is shielded by the underlying layers. ...
CCNA1 Complete Lecture Set Mod 1 to 11
... design new networks, and understand the Internet. A networking professional must understand the tremendous impact of bandwidth and throughput on network performance and design. The demand for bandwidth continues to grow. As soon as new network technologies and infrastructures are built to provide gr ...
... design new networks, and understand the Internet. A networking professional must understand the tremendous impact of bandwidth and throughput on network performance and design. The demand for bandwidth continues to grow. As soon as new network technologies and infrastructures are built to provide gr ...
Machine-to-Machine (M2M) Gateway: Trusted and Connected
... Machine-to-Machine (M2M) Gateway: Trusted and Connected Intelligence ...
... Machine-to-Machine (M2M) Gateway: Trusted and Connected Intelligence ...
TR-M2M-0009v0.7.0 oneM2M Protocol Analysis
... This is a draft oneM2M document and should not be relied upon; the final version, if any, will be made available by oneM2M Partners Type 1. ...
... This is a draft oneM2M document and should not be relied upon; the final version, if any, will be made available by oneM2M Partners Type 1. ...
Protocol Analysis
... This is a draft oneM2M document and should not be relied upon; the final version, if any, will be made available by oneM2M Partners Type 1. ...
... This is a draft oneM2M document and should not be relied upon; the final version, if any, will be made available by oneM2M Partners Type 1. ...
Linux+ Guide to Linux Certification
... – Attempts to avoid collisions altogether – Time when most collisions occur is immediately after a station completes transmission – All stations must wait random amount of time after ...
... – Attempts to avoid collisions altogether – Time when most collisions occur is immediately after a station completes transmission – All stations must wait random amount of time after ...
old_Ch3
... It was designed to allow for dynamic routing: – different types of metrics can be used to define the “shortest” path, e.g., delay, link utilization, physical distance, link bit rate, etc. ...
... It was designed to allow for dynamic routing: – different types of metrics can be used to define the “shortest” path, e.g., delay, link utilization, physical distance, link bit rate, etc. ...
3rd Edition, Chapter 5 - Department of Computer and Information
... Ethernet CSMA/CD algorithm 1. NIC receives datagram from network layer, creates frame 2. If NIC senses channel idle, starts frame transmission. If NIC senses channel busy, waits until channel idle, then transmits. 3. If NIC transmits entire frame without detecting another transmission, NIC is done ...
... Ethernet CSMA/CD algorithm 1. NIC receives datagram from network layer, creates frame 2. If NIC senses channel idle, starts frame transmission. If NIC senses channel busy, waits until channel idle, then transmits. 3. If NIC transmits entire frame without detecting another transmission, NIC is done ...
Appendix
... independence can be extended to more than 2 vectors If vectors are linearly independent, then none of them can be written as a linear combination of the others o None of the independent vectors is a ...
... independence can be extended to more than 2 vectors If vectors are linearly independent, then none of them can be written as a linear combination of the others o None of the independent vectors is a ...
Chapter 5 on Link/MAC Layer - Department of Computer and
... Ethernet CSMA/CD algorithm 1. NIC receives datagram from network layer, creates frame 2. If NIC senses channel idle, starts frame transmission. If NIC senses channel busy, waits until channel idle, then transmits. 3. If NIC transmits entire frame without detecting another transmission, NIC is done ...
... Ethernet CSMA/CD algorithm 1. NIC receives datagram from network layer, creates frame 2. If NIC senses channel idle, starts frame transmission. If NIC senses channel busy, waits until channel idle, then transmits. 3. If NIC transmits entire frame without detecting another transmission, NIC is done ...
3rd Edition, Chapter 5
... transportation mode = link layer protocol travel agent = routing algorithm 5: DataLink Layer ...
... transportation mode = link layer protocol travel agent = routing algorithm 5: DataLink Layer ...
Link Layer
... encapsulate datagram into frame, adding header, trailer ‘physical addresses’ used in frame headers to identify source, destination • different from IP address! Link access Media access control (MAC) protocol Coordinate the frame transmissions of many nodes if multiple nodes share a medium ...
... encapsulate datagram into frame, adding header, trailer ‘physical addresses’ used in frame headers to identify source, destination • different from IP address! Link access Media access control (MAC) protocol Coordinate the frame transmissions of many nodes if multiple nodes share a medium ...
bca501 : core – 18 : computer networks
... hooked onto the next outgoing data frame is called a) piggybacking b) cyclic redundancy check c) fletcher’s checksum d) none of the mentioned Answer: a. 34. Transport layer aggregates data from different applications into a single stream before passing it to a) network layer b) data link layer c) ap ...
... hooked onto the next outgoing data frame is called a) piggybacking b) cyclic redundancy check c) fletcher’s checksum d) none of the mentioned Answer: a. 34. Transport layer aggregates data from different applications into a single stream before passing it to a) network layer b) data link layer c) ap ...
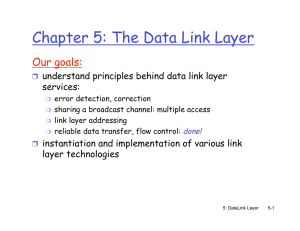
Chapter 5: The Data Link Layer
... 5.6 Hubs and switches ❒ 5.7 PPP ❒ 5.8 Link Virtualization: ATM and MPLS ...
... 5.6 Hubs and switches ❒ 5.7 PPP ❒ 5.8 Link Virtualization: ATM and MPLS ...
TR50-20101006-011_ALU__TR
... Location Specific Trigger – Used to trigger M2M devices that are known by the M2M Application to be in a particular area or location. ...
... Location Specific Trigger – Used to trigger M2M devices that are known by the M2M Application to be in a particular area or location. ...