david-meyer-lisp-network-grow-ietf72-2008
... – The ALT typically runs over GRE tunnels, but we also have it running over native and .1q ethernet encapsulations ...
... – The ALT typically runs over GRE tunnels, but we also have it running over native and .1q ethernet encapsulations ...
N150 Wireless ADSL2+ Modem Router DGN1000 User Manual 350 East Plumeria Drive
... way to set up a wireless home network with fast access to the Internet over a high-speed digital subscriber line (DSL). It has a built-in DSL modem, is compatible with all major DSL Internet service providers, lets you block unsafe Internet content and applications, and protects the devices (PCs, ga ...
... way to set up a wireless home network with fast access to the Internet over a high-speed digital subscriber line (DSL). It has a built-in DSL modem, is compatible with all major DSL Internet service providers, lets you block unsafe Internet content and applications, and protects the devices (PCs, ga ...
Top-Down Network Design
... The publisher offers excellent discounts on this book when ordered in quantity for bulk purchases or special sales, which may include electronic versions and/or custom covers and content particular to your business, training goals, marketing focus, and branding interests. For more information, pleas ...
... The publisher offers excellent discounts on this book when ordered in quantity for bulk purchases or special sales, which may include electronic versions and/or custom covers and content particular to your business, training goals, marketing focus, and branding interests. For more information, pleas ...
SpeedStream™ Router Family
... All other trademarks and registered trademarks mentioned in this manual are the sole property of their respective companies. ...
... All other trademarks and registered trademarks mentioned in this manual are the sole property of their respective companies. ...
Practical BGP
... The BGP Peering Process ...................................................................................................................... 20 BGP Attributes ........................................................................................................................................... ...
... The BGP Peering Process ...................................................................................................................... 20 BGP Attributes ........................................................................................................................................... ...
N450 WiFi Cable Modem Router N450/CG2000Dv2 User Manual
... Position Your Modem Router The modem router lets you access your network anywhere within the operating range of your wireless network. However, the operating distance or range of your wireless connection can vary significantly depending on the physical placement of your modem router. For example, th ...
... Position Your Modem Router The modem router lets you access your network anywhere within the operating range of your wireless network. However, the operating distance or range of your wireless connection can vary significantly depending on the physical placement of your modem router. For example, th ...
Presentation Title Size 30PT
... Teaching Tip If students have trouble seeing why only one double colon is allowed, give them an example of what would happen if you allowed it. The following two addresses could both be shortened to the third address, so there would be ambiguity ...
... Teaching Tip If students have trouble seeing why only one double colon is allowed, give them an example of what would happen if you allowed it. The following two addresses could both be shortened to the third address, so there would be ambiguity ...
Compatible Systems Reference Guides
... The default passwords as shipped from the factory are letmein. It is strongly recommended that the password be changed using the [ General ] section. Once the passwords are set, the same passwords are used by CompatiView. Modes of Operation There are two modes of operation in the Command Line interf ...
... The default passwords as shipped from the factory are letmein. It is strongly recommended that the password be changed using the [ General ] section. Once the passwords are set, the same passwords are used by CompatiView. Modes of Operation There are two modes of operation in the Command Line interf ...
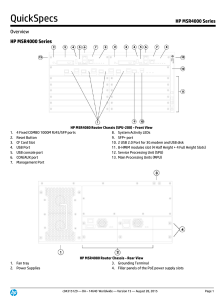
HP MSR4000 Series
... VXLAN (Virtual eXtensible LAN, scalable virtual local area network) is an IP-based network, using the "MAC in UDP" package of Layer VPN technology. VXLAN can be based on an existing ISP or enterprise IP networks for decentralized physical site provides Layer 2 communication, and can provide service ...
... VXLAN (Virtual eXtensible LAN, scalable virtual local area network) is an IP-based network, using the "MAC in UDP" package of Layer VPN technology. VXLAN can be based on an existing ISP or enterprise IP networks for decentralized physical site provides Layer 2 communication, and can provide service ...
D1.1: Functional Architecture Definition and Top Level
... TEQUILA’s main objective is to study, specify, implement and validate service definition and Traffic Engineering (TE) tools for the Internet. The TEQUILA system should provide both quantitative and qualitative service guarantees through planning, dimensioning and dynamic control of traffic managemen ...
... TEQUILA’s main objective is to study, specify, implement and validate service definition and Traffic Engineering (TE) tools for the Internet. The TEQUILA system should provide both quantitative and qualitative service guarantees through planning, dimensioning and dynamic control of traffic managemen ...
AMHS Connectivity - Airports Authority of India
... Transport Layer Transport Protocol Class 0 (TP0) RFC 1006 / RFC 2126 ...
... Transport Layer Transport Protocol Class 0 (TP0) RFC 1006 / RFC 2126 ...
PAN‐OS Web Interface Reference Guide
... and receive traffic at different transmission rates. You can configure Ethernet interfaces as the following types: tap, high availability (HA), log card (interface and subinterface), decrypt mirror, virtual wire (interface and subinterface), Layer 2 (interface and subinterface), Layer 3 (interface ...
... and receive traffic at different transmission rates. You can configure Ethernet interfaces as the following types: tap, high availability (HA), log card (interface and subinterface), decrypt mirror, virtual wire (interface and subinterface), Layer 2 (interface and subinterface), Layer 3 (interface ...
Analysis of Reliable Multicast Protocols
... 64 bytes from tiptoe.fhda.edu (153.18.8.1): icmp_seq=5 ttl=62 time=2.00 ms 64 bytes from tiptoe.fhda.edu (153.18.8.1): icmp_seq=6 ttl=62 time=1.94 ms 64 bytes from tiptoe.fhda.edu (153.18.8.1): icmp_seq=7 ttl=62 time=1.94 ms 64 bytes from tiptoe.fhda.edu (153.18.8.1): icmp_seq=8 ttl=62 time=1.97 ms ...
... 64 bytes from tiptoe.fhda.edu (153.18.8.1): icmp_seq=5 ttl=62 time=2.00 ms 64 bytes from tiptoe.fhda.edu (153.18.8.1): icmp_seq=6 ttl=62 time=1.94 ms 64 bytes from tiptoe.fhda.edu (153.18.8.1): icmp_seq=7 ttl=62 time=1.94 ms 64 bytes from tiptoe.fhda.edu (153.18.8.1): icmp_seq=8 ttl=62 time=1.97 ms ...
ROUTE Chapter 3
... • Depending on where it resides in Area 0, it may also be called an Internal router, an ABR, or an ASBR. ...
... • Depending on where it resides in Area 0, it may also be called an Internal router, an ABR, or an ASBR. ...
profesores.usfq.edu.ec
... • Depending on where it resides in Area 0, it may also be called an Internal router, an ABR, or an ASBR. ...
... • Depending on where it resides in Area 0, it may also be called an Internal router, an ABR, or an ASBR. ...
Command Line Interface Guide
... This guide is intended to help you configure and manage the router using the Command Line Interface. The guide assumes that you have read the information about the router and installed the hardware using the Internet Quick Start Guide. The guide is divided into eight parts: Introduction. Describes t ...
... This guide is intended to help you configure and manage the router using the Command Line Interface. The guide assumes that you have read the information about the router and installed the hardware using the Internet Quick Start Guide. The guide is divided into eight parts: Introduction. Describes t ...
Chapter 8: Virtual LAN (VLAN)
... – Easily change the LAN configuration. – Easily control network traffic. – Improve security. ...
... – Easily change the LAN configuration. – Easily control network traffic. – Improve security. ...
Complete PDF manual
... Viewing a List of Attached Devices .................................................................................6-6 Managing the Configuration File .....................................................................................6-6 Backing Up and Restoring the Configuration ................ ...
... Viewing a List of Attached Devices .................................................................................6-6 Managing the Configuration File .....................................................................................6-6 Backing Up and Restoring the Configuration ................ ...
NETGEAR Wireless-N Router WNR2000 User Manual , Inc.
... NETGEAR and the NETGEAR logo are registered trademarks, and RangeMax and Smart Wizard are trademarks of NETGEAR. Inc. in the United States and/or other countries. Microsoft, Windows, and Windows NT are registered trademarks and Windows Vista is a trademark of Microsoft Corporation. Other brand and p ...
... NETGEAR and the NETGEAR logo are registered trademarks, and RangeMax and Smart Wizard are trademarks of NETGEAR. Inc. in the United States and/or other countries. Microsoft, Windows, and Windows NT are registered trademarks and Windows Vista is a trademark of Microsoft Corporation. Other brand and p ...
Paper Title (use style: paper title)
... provides both one-to-many and many-to-many multicasting capabilities as it builds a shared unidirectional shared tree rooted on a Rendezvous Point, however the switching mechanism from the Rendezvous Point shared tree to a sourcerouted shortest path tree is inadequate for many-to-many communications ...
... provides both one-to-many and many-to-many multicasting capabilities as it builds a shared unidirectional shared tree rooted on a Rendezvous Point, however the switching mechanism from the Rendezvous Point shared tree to a sourcerouted shortest path tree is inadequate for many-to-many communications ...
Analysis of Reliable Multicast Protocols
... 64 bytes from tiptoe.fhda.edu (153.18.8.1): icmp_seq=5 ttl=62 time=2.00 ms 64 bytes from tiptoe.fhda.edu (153.18.8.1): icmp_seq=6 ttl=62 time=1.94 ms 64 bytes from tiptoe.fhda.edu (153.18.8.1): icmp_seq=7 ttl=62 time=1.94 ms 64 bytes from tiptoe.fhda.edu (153.18.8.1): icmp_seq=8 ttl=62 time=1.97 ms ...
... 64 bytes from tiptoe.fhda.edu (153.18.8.1): icmp_seq=5 ttl=62 time=2.00 ms 64 bytes from tiptoe.fhda.edu (153.18.8.1): icmp_seq=6 ttl=62 time=1.94 ms 64 bytes from tiptoe.fhda.edu (153.18.8.1): icmp_seq=7 ttl=62 time=1.94 ms 64 bytes from tiptoe.fhda.edu (153.18.8.1): icmp_seq=8 ttl=62 time=1.97 ms ...
Thwarting E-mail Spam Laundering - Computer Science
... Spammers have plagued the Internet by exploiting a large number of spam proxies. The facility of breaking spam laundering and deterring spamming activities close to their sources, which would greatly benefit not only e-mail users but also victim ISPs, is in great demand but still missing. In this ar ...
... Spammers have plagued the Internet by exploiting a large number of spam proxies. The facility of breaking spam laundering and deterring spamming activities close to their sources, which would greatly benefit not only e-mail users but also victim ISPs, is in great demand but still missing. In this ar ...