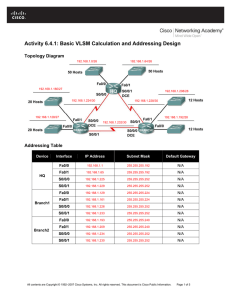
Activity 6.4.1: Basic VLSM Calculation and Addressing Design
... 4. What is the maximum number of host IP addresses that are needed for a single subnet? _______ 5. What is the least number of host IP addresses that are needed for a single subnet? _______ 6. How many IP addresses are needed for the East portion of the network? Be sure to include the WAN links betw ...
... 4. What is the maximum number of host IP addresses that are needed for a single subnet? _______ 5. What is the least number of host IP addresses that are needed for a single subnet? _______ 6. How many IP addresses are needed for the East portion of the network? Be sure to include the WAN links betw ...
Ip Addressing and Subnetting Workbook v1_2.pmd
... When you take a single network such as 192.100.10.0 and divide it into five smaller networks (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five smaller subnetworks. Each ...
... When you take a single network such as 192.100.10.0 and divide it into five smaller networks (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five smaller subnetworks. Each ...
CIS 175 Lecture Notes
... o Connection must be less than 50 feet o Data represented by voltages between +15v and -15v o 25-pin connector, with specific signals such as data, ground and control assigned to designated pins o Specifies transmission of characters between, e.g., a terminal and a modem Transmitter never leaves wir ...
... o Connection must be less than 50 feet o Data represented by voltages between +15v and -15v o 25-pin connector, with specific signals such as data, ground and control assigned to designated pins o Specifies transmission of characters between, e.g., a terminal and a modem Transmitter never leaves wir ...
Computer Networks and Internets By Douglas E Comer
... o Connection must be less than 50 feet o Data represented by voltages between +15v and -15v o 25-pin connector, with specific signals such as data, ground and control assigned to designated pins o Specifies transmission of characters between, e.g., a terminal and a modem Transmitter never leaves wir ...
... o Connection must be less than 50 feet o Data represented by voltages between +15v and -15v o 25-pin connector, with specific signals such as data, ground and control assigned to designated pins o Specifies transmission of characters between, e.g., a terminal and a modem Transmitter never leaves wir ...
Ip Addressing and Subnetting Workbook
... (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five smaller subnetworks. Each independent of the other. This can only be accomplished by using a custom subnet mask. A cus ...
... (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five smaller subnetworks. Each independent of the other. This can only be accomplished by using a custom subnet mask. A cus ...
Ip Addressing and Subnetting Workbook
... When you take a single network such as 192.100.10.0 and divide it into five smaller networks (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five smaller subnetworks. Each ...
... When you take a single network such as 192.100.10.0 and divide it into five smaller networks (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five smaller subnetworks. Each ...
Ip Addressing and Subnetting Workbook
... When you take a single network such as 192.100.10.0 and divide it into five smaller networks (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five smaller subnetworks. Each ...
... When you take a single network such as 192.100.10.0 and divide it into five smaller networks (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five smaller subnetworks. Each ...
IEEE 1588, Standard for a Precision Clock Synchronization
... The project P1588 was started in order to specify the version 2 of the protocol. IEEE 1588 – 2008 was approved 27th of March 2008. Commercial version 2 enabled products, protocol stacks, and IPs are available. Components with integrated IEEE 1588 hardware assistance were announced or are ava ...
... The project P1588 was started in order to specify the version 2 of the protocol. IEEE 1588 – 2008 was approved 27th of March 2008. Commercial version 2 enabled products, protocol stacks, and IPs are available. Components with integrated IEEE 1588 hardware assistance were announced or are ava ...
Universal Plug and Play Machine Models
... Recently, Microsoft took a lead in the development of a standard for peer-to-peer network connectivity of various intelligent appliances, wireless devices and PCs. The current version of the standard is Universal Plug and Play (UPnP) Device Architecture V 1.0 defined in [1]; see also the website [2] ...
... Recently, Microsoft took a lead in the development of a standard for peer-to-peer network connectivity of various intelligent appliances, wireless devices and PCs. The current version of the standard is Universal Plug and Play (UPnP) Device Architecture V 1.0 defined in [1]; see also the website [2] ...
MAC address
... the foreseeable future. A locally administered address is assigned to a device by a network administrator, overriding the burned-in address. Locally administered addresses do not contain OUIs.
... the foreseeable future. A locally administered address is assigned to a device by a network administrator, overriding the burned-in address. Locally administered addresses do not contain OUIs.
Universally administered and locally administered addresses are distinguished by setting the second& ...
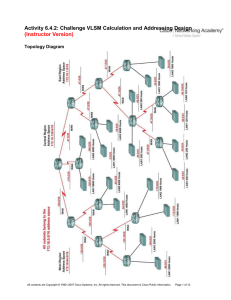
2e_06_6_4_2_vlsm_instr
... Task 3: Design an IP Addressing Scheme for the Central Network. Step 1: Determine the subnet information for the Central LAN1. Use the address space that was designated for the Central network in Task 1. 1. What is the smallest size subnet that can be used to meet this requirement? _______ /19 2. Wh ...
... Task 3: Design an IP Addressing Scheme for the Central Network. Step 1: Determine the subnet information for the Central LAN1. Use the address space that was designated for the Central network in Task 1. 1. What is the smallest size subnet that can be used to meet this requirement? _______ /19 2. Wh ...
project report
... the differences between the two, and the problems encountered in setting them up. Chapter five will cover an area of IPv6 that isn't possible to test due to practical reasons (not having a dedicated subnet), but are very important to the transition to IPv6 Routing Protocols and Domain Name Service ( ...
... the differences between the two, and the problems encountered in setting them up. Chapter five will cover an area of IPv6 that isn't possible to test due to practical reasons (not having a dedicated subnet), but are very important to the transition to IPv6 Routing Protocols and Domain Name Service ( ...
Deploying the Dell Force10 MXL into a Cisco Nexus Network
... Uplink configuration for the MXL will generally be done in one of two ways in a Cisco Nexus network environment: running PVST with discreet LAGs connected to separate top-of-rack switches as covered in Trunk Port Uplink Configuration with Per-VLAN Spanning Tree and running PVST with a single LAG con ...
... Uplink configuration for the MXL will generally be done in one of two ways in a Cisco Nexus network environment: running PVST with discreet LAGs connected to separate top-of-rack switches as covered in Trunk Port Uplink Configuration with Per-VLAN Spanning Tree and running PVST with a single LAG con ...
Multicasting
... (DR), is a router that agrees to cache copies of the data and process acknowledgements from routers and hosts further down the forwarding tree. If a retransmission is need it is taken from the routers cache. This occurs when the host or router send a NACK. The NACK will propogate up the tree until a ...
... (DR), is a router that agrees to cache copies of the data and process acknowledgements from routers and hosts further down the forwarding tree. If a retransmission is need it is taken from the routers cache. This occurs when the host or router send a NACK. The NACK will propogate up the tree until a ...
Overlay Network
... All overlay protocols that must be able to compute: Given the logical address of some overlay node R, each overlay node with logical address A must be able to compute the logical address of A’s parent and child nodes in an embedded tree which has R as the root. Denali Retreat, April 2002 ...
... All overlay protocols that must be able to compute: Given the logical address of some overlay node R, each overlay node with logical address A must be able to compute the logical address of A’s parent and child nodes in an embedded tree which has R as the root. Denali Retreat, April 2002 ...
ATM LAN Emulation
... ATM adapter card needs to support the relevant type of logical subnet. New Applications ...
... ATM adapter card needs to support the relevant type of logical subnet. New Applications ...
Tsunami 8000 Series (Point-to-point and Point-to
... © 2013 Proxim Wireless Corporation, Milpitas, CA. All rights reserved. Covered by one or more of the following U.S. patents: 5,231,634; 5,875,179; 6,006,090; 5,809,060; 6,075,812; 5,077,753. The content described herein are copyrighted with all rights reserved. No part of this publication may be rep ...
... © 2013 Proxim Wireless Corporation, Milpitas, CA. All rights reserved. Covered by one or more of the following U.S. patents: 5,231,634; 5,875,179; 6,006,090; 5,809,060; 6,075,812; 5,077,753. The content described herein are copyrighted with all rights reserved. No part of this publication may be rep ...
PDF - Complete Book (3.05 MB)
... network traffic profile. This profile can then be referenced by Cisco IOS XR software features such as traffic filtering, route filtering, QoS classification, and access control. There are 2 types of ACLs: • Standard ACLs- Verifies only source addresses of the packets. Standard ACLs control traffic ...
... network traffic profile. This profile can then be referenced by Cisco IOS XR software features such as traffic filtering, route filtering, QoS classification, and access control. There are 2 types of ACLs: • Standard ACLs- Verifies only source addresses of the packets. Standard ACLs control traffic ...
The Java and Jini Technologies for Distance Education in
... Multicast : One to Many Multicast is communication between a single host and multiple receivers. ...
... Multicast : One to Many Multicast is communication between a single host and multiple receivers. ...
ROUTE Chapter 8 - Strona startowa
... The first 64 bits are the network portion of the address and are statically specified or learned via SLAAC. The interface ID (second 64-bits) is the host portion of the address and is automatically generated by the router or host device. The interface ID on an Ethernet link is based on the 48- ...
... The first 64 bits are the network portion of the address and are statically specified or learned via SLAAC. The interface ID (second 64-bits) is the host portion of the address and is automatically generated by the router or host device. The interface ID on an Ethernet link is based on the 48- ...
Introduction to IPv6 protocol
... – to determine the link-layer @ of a neighbor – or to check its impeachability – also used to detect duplicate addresses (DAD) ...
... – to determine the link-layer @ of a neighbor – or to check its impeachability – also used to detect duplicate addresses (DAD) ...
Inferring Subnets in Router-Level Topology Collection Studies
... Based on this observation, we use an iterative approach to identify candidate subnets. We first form all candidate /x subnets from the data set by combining the IP addresses whose first x bits match. Next, we recursively form smaller subnets (e.g., /x, /(x+1), . . ., /31 subnets). At this point, we ...
... Based on this observation, we use an iterative approach to identify candidate subnets. We first form all candidate /x subnets from the data set by combining the IP addresses whose first x bits match. Next, we recursively form smaller subnets (e.g., /x, /(x+1), . . ., /31 subnets). At this point, we ...
Inferring Subnets in Router-level Topology Collection Studies
... Based on this observation, we use an iterative approach to identify candidate subnets. We first form all candidate /x subnets from the data set by combining the IP addresses whose first x bits match. Next, we recursively form smaller subnets (e.g., /x, /(x+1), . . ., /31 subnets). At this point, we ...
... Based on this observation, we use an iterative approach to identify candidate subnets. We first form all candidate /x subnets from the data set by combining the IP addresses whose first x bits match. Next, we recursively form smaller subnets (e.g., /x, /(x+1), . . ., /31 subnets). At this point, we ...
I²C
I²C (Inter-Integrated Circuit), pronounced I-squared-C, is a multi-master, multi-slave, single-ended, serial computer bus invented by Philips Semiconductor (now NXP Semiconductors). It is typically used for attaching lower-speed peripheral ICs to processors and microcontrollers. Alternatively I²C is spelled I2C (pronounced I-two-C) or IIC (pronounced I-I-C). Since October 10, 2006, no licensing fees are required to implement the I²C protocol. However, fees are still required to obtain I²C slave addresses allocated by NXP.Several competitors, such as Siemens AG (later Infineon Technologies AG, now Intel mobile communications), NEC, Texas Instruments, STMicroelectronics (formerly SGS-Thomson), Motorola (later Freescale), and Intersil, have introduced compatible I²C products to the market since the mid-1990s.SMBus, defined by Intel in 1995, is a subset of I²C that defines the protocols more strictly. One purpose of SMBus is to promote robustness and interoperability. Accordingly, modern I²C systems incorporate policies and rules from SMBus, sometimes supporting both I²C and SMBus, requiring only minimal reconfiguration.