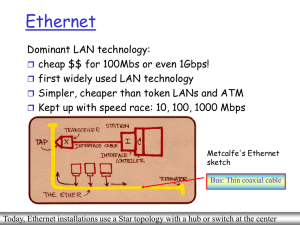
Ethernet - College of DuPage
... –The original Ethernet standard defined the minimum frame size as 64 bytes and the maximum as 1518 bytes. –This includes all bytes from the Destination MAC Address field through the Frame Check Sequence (FCS) field. –The Preamble and Start Frame Delimiter fields are not included when describing the ...
... –The original Ethernet standard defined the minimum frame size as 64 bytes and the maximum as 1518 bytes. –This includes all bytes from the Destination MAC Address field through the Frame Check Sequence (FCS) field. –The Preamble and Start Frame Delimiter fields are not included when describing the ...
Ethernet
... –The original Ethernet standard defined the minimum frame size as 64 bytes and the maximum as 1518 bytes. –This includes all bytes from the Destination MAC Address field through the Frame Check Sequence (FCS) field. –The Preamble and Start Frame Delimiter fields are not included when describing the ...
... –The original Ethernet standard defined the minimum frame size as 64 bytes and the maximum as 1518 bytes. –This includes all bytes from the Destination MAC Address field through the Frame Check Sequence (FCS) field. –The Preamble and Start Frame Delimiter fields are not included when describing the ...
PPT Version
... path computation may be made by PCE physically distinct from the computed path path computed by PCE may be complete: full explicit path of strict hops partial: mix of strict & loose hops (may be an abstract node such as an AS) PCE path computation can be used in conjunction with other path ...
... path computation may be made by PCE physically distinct from the computed path path computed by PCE may be complete: full explicit path of strict hops partial: mix of strict & loose hops (may be an abstract node such as an AS) PCE path computation can be used in conjunction with other path ...
The Internet and Its Uses
... Frame Check Sequence Field (4 bytes) –It detects errors in a frame. The receiving device receives the frame and generates a CRC to look for errors. If the calculations do not match, the frame is dropped. Cisco Public ITE 1 Chapter 6 © 2006 Cisco Systems, Inc. All rights reserved. ...
... Frame Check Sequence Field (4 bytes) –It detects errors in a frame. The receiving device receives the frame and generates a CRC to look for errors. If the calculations do not match, the frame is dropped. Cisco Public ITE 1 Chapter 6 © 2006 Cisco Systems, Inc. All rights reserved. ...
Network Performance Definitions - Network Startup Resource Center
... The smallest value that is larger than 95% of the values in a given sample This means that 95% of the time the channel utilization is equal to or less than this value Or ...
... The smallest value that is larger than 95% of the values in a given sample This means that 95% of the time the channel utilization is equal to or less than this value Or ...
ITE PC v4.0 Chapter 1
... Identifier of the sender’s location Salutation or greeting Recipient identifier The message content Source identifier End of message indicator ...
... Identifier of the sender’s location Salutation or greeting Recipient identifier The message content Source identifier End of message indicator ...
Chapter 3: Network Protocols and Communications
... Identifier of the recipient’s location Identifier of the sender’s location Salutation or greeting Recipient identifier The message content Source identifier End of message indicator ...
... Identifier of the recipient’s location Identifier of the sender’s location Salutation or greeting Recipient identifier The message content Source identifier End of message indicator ...
Command Line Interface
... Replacing a Multiplexer Uplink Module (MUM) Paradyne recommends clearing the NVRAM of a previously configured MUM before using it as a replacement in a different chassis. Once NVRAM has been cleared, the MUM will revert to original default settings. Then chassis and interface module configurations w ...
... Replacing a Multiplexer Uplink Module (MUM) Paradyne recommends clearing the NVRAM of a previously configured MUM before using it as a replacement in a different chassis. Once NVRAM has been cleared, the MUM will revert to original default settings. Then chassis and interface module configurations w ...
multicast
... – Traffic Flooded throughout network – Pruned back where it is unwanted – Flood & Prune behavior (typically every 3 minutes) ...
... – Traffic Flooded throughout network – Pruned back where it is unwanted – Flood & Prune behavior (typically every 3 minutes) ...
Cisco Discovery Protocol (CDP)
... Primary use of CDP is to discover all Cisco devices that are directly connected to a local device. This is done by transmitting type length values (TLVs) which are blocks of information embedded in CDP advertisements. To display the CDP information, use the command: show cdp Shows information that c ...
... Primary use of CDP is to discover all Cisco devices that are directly connected to a local device. This is done by transmitting type length values (TLVs) which are blocks of information embedded in CDP advertisements. To display the CDP information, use the command: show cdp Shows information that c ...
Connection-oriented internetworking
... Difference between LSP encoding type, switching type and GPID – Switching type: type of multiplexing used on the links of an end-to-end LSP. 3471 states “This field normally is consistent across all links of an LSP.” • e.g., TDM, PSC-1 – LSP encoding type: type of data carried on each link of the LS ...
... Difference between LSP encoding type, switching type and GPID – Switching type: type of multiplexing used on the links of an end-to-end LSP. 3471 states “This field normally is consistent across all links of an LSP.” • e.g., TDM, PSC-1 – LSP encoding type: type of data carried on each link of the LS ...
PDF
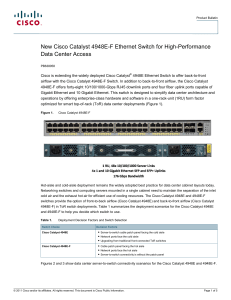
... Cisco Services makes networks, applications, and the people who use them work better together. Today, the network is a strategic platform in a world that demands better integration of people, information, and ideas. The network works better when services, together with products, create solutions ali ...
... Cisco Services makes networks, applications, and the people who use them work better together. Today, the network is a strategic platform in a world that demands better integration of people, information, and ideas. The network works better when services, together with products, create solutions ali ...
Presentation
... Require standard OS and application set for antivirus protection on all PCs and use automated desktop management software to allow for responsive remediation of infected devices Require RFC1918 space for all labs, use a proxy server to access the Internet, provide virus filtering at the edge usi ...
... Require standard OS and application set for antivirus protection on all PCs and use automated desktop management software to allow for responsive remediation of infected devices Require RFC1918 space for all labs, use a proxy server to access the Internet, provide virus filtering at the edge usi ...
HPE 5900 Switch Series
... • Access control lists (ACLs) provide IP Layer 3 filtering based on source/destination IP address/subnet and source/ destination TCP/UDP port number • RADIUS/TACACS+ eases switch management security administration by using a password authentication server • Secure Shell encrypts all transmitted data ...
... • Access control lists (ACLs) provide IP Layer 3 filtering based on source/destination IP address/subnet and source/ destination TCP/UDP port number • RADIUS/TACACS+ eases switch management security administration by using a password authentication server • Secure Shell encrypts all transmitted data ...
Setup Wizard
... POTS splitter with a RJ11 connection cable. Connection to LAN port To connect to a hub or PC, use a RJ45 cable. You can connect the router to up to four LAN devices. The ports are auto-sensing MDI/X and either straight-through cable or crossover cable can be used. Connection to USB port Connect the ...
... POTS splitter with a RJ11 connection cable. Connection to LAN port To connect to a hub or PC, use a RJ45 cable. You can connect the router to up to four LAN devices. The ports are auto-sensing MDI/X and either straight-through cable or crossover cable can be used. Connection to USB port Connect the ...
PDF
... All contents are Copyright © 2007-2008 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information. ...
... All contents are Copyright © 2007-2008 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information. ...
FS980M Datasheet
... tools that provides a simplified approach to network management. Common tasks are automated, or made so simple, that your network can run without the need for highly-trained and expensive network engineers. Powerful features like centralized management, auto-backup, autoupgrade, auto-provisioning an ...
... tools that provides a simplified approach to network management. Common tasks are automated, or made so simple, that your network can run without the need for highly-trained and expensive network engineers. Powerful features like centralized management, auto-backup, autoupgrade, auto-provisioning an ...
Network Performance Analysis
... IPv4 53603 TCP localhost.localdomain:x11-ssh-offset (LISTEN) IPv6 53604 TCP [::1]:x11-ssh-offset (LISTEN) ...
... IPv4 53603 TCP localhost.localdomain:x11-ssh-offset (LISTEN) IPv6 53604 TCP [::1]:x11-ssh-offset (LISTEN) ...
In Search of Path Diversity in ISP Networks ABSTRACT
... between the number of link- and PoP-disjoint paths is expected because there are multiple links connecting a pair of PoPs. The number of link-disjoint paths is relatively large. Almost 90% of pairs of PoPs have at least four link-disjoint paths between them, and 40% of pairs of PoPs are connected th ...
... between the number of link- and PoP-disjoint paths is expected because there are multiple links connecting a pair of PoPs. The number of link-disjoint paths is relatively large. Almost 90% of pairs of PoPs have at least four link-disjoint paths between them, and 40% of pairs of PoPs are connected th ...
Ethernet Switches
... multi-tier throughput same as single segment throughput individual LAN restrictions pose limits on number of nodes in same collision domain and on total allowed geographical coverage cannot connect different Ethernet types (e.g., 10BaseT and 100baseT) ...
... multi-tier throughput same as single segment throughput individual LAN restrictions pose limits on number of nodes in same collision domain and on total allowed geographical coverage cannot connect different Ethernet types (e.g., 10BaseT and 100baseT) ...
performance-analysis
... IPv4 53603 TCP localhost.localdomain:x11-ssh-offset (LISTEN) IPv6 53604 TCP [::1]:x11-ssh-offset (LISTEN) ...
... IPv4 53603 TCP localhost.localdomain:x11-ssh-offset (LISTEN) IPv6 53604 TCP [::1]:x11-ssh-offset (LISTEN) ...
Introduction - Communications
... Types of Multicast addresses • The range of addresses between 224.0.0.0 and 224.0.0.255, inclusive, is reserved for the use of routing protocols and other low-level topology discovery or maintenance protocols • Multicast routers should not forward any multicast datagram with destination addresses i ...
... Types of Multicast addresses • The range of addresses between 224.0.0.0 and 224.0.0.255, inclusive, is reserved for the use of routing protocols and other low-level topology discovery or maintenance protocols • Multicast routers should not forward any multicast datagram with destination addresses i ...
CISCO GIGABIT ETHERNET NETWORK MODULE
... This network module has one gigabit interface converter (GBIC) slot to carry any standard copper or optical Cisco GBIC (see Table 1 for details). The flexibility to use different GBICs allows for making a choice depending on various factors, such as distance, cost, existing infrastructure, future ex ...
... This network module has one gigabit interface converter (GBIC) slot to carry any standard copper or optical Cisco GBIC (see Table 1 for details). The flexibility to use different GBICs allows for making a choice depending on various factors, such as distance, cost, existing infrastructure, future ex ...
Spanning Tree Protocol
The Spanning Tree Protocol (STP) is an older network protocol that ensures a loop-free topology for any bridged Ethernet local area network. The basic function of STP is to prevent bridge loops and the broadcast radiation that results from them. Spanning tree also allows a network design to include spare (redundant) links to provide automatic backup paths if an active link fails, without the danger of bridge loops, or the need for manual enabling/disabling of these backup links.Spanning Tree Protocol (STP) was originally standardized as IEEE 802.1D, in 802.1d-1998, but much of the functionality (spanning tree, rapid spanning tree, multiple spanning tree) previously specified in 802.1D, 801.1s, 802.1w has been incorporated into IEEE 802.1Q-2014 which includes shortest path bridging, the IEEE sanctioned replacement for these spanning tree functions.As the name suggests, it creates a spanning tree within a network of connected layer-2 bridges (typically Ethernet switches), and disables those links that are not part of the spanning tree, leaving a single active path between any two network nodes. STP is based on an algorithm that was invented by Radia Perlman while she was working for Digital Equipment Corporation.