Analysis of Algorithms
... log2n! for any comparison-based sorting algorithm, since the longest path represents the worst case and its length is the height log2n! n log2n (by Sterling approximation) This lower bound is tight (mergesort or heapsort) Ex. Prove that 5 (or 7) comparisons are necessary and sufficient for sor ...
... log2n! for any comparison-based sorting algorithm, since the longest path represents the worst case and its length is the height log2n! n log2n (by Sterling approximation) This lower bound is tight (mergesort or heapsort) Ex. Prove that 5 (or 7) comparisons are necessary and sufficient for sor ...
Chapter 2: Fundamentals of the Analysis of Algorithm Efficiency
... Prepare a program implementing the algorithm (or algorithms) for the experimentation Generate a sample of inputs Run the algorithm (or algorithms) on the sample’s inputs and record the data observed Analyze the data obtained ...
... Prepare a program implementing the algorithm (or algorithms) for the experimentation Generate a sample of inputs Run the algorithm (or algorithms) on the sample’s inputs and record the data observed Analyze the data obtained ...
DATA STRUCTURES - University of Cape Town
... A list of one or more words is called a chain when each word in that list, except the first, is obtained from the preceding word by appending one or more letters on the right. For instance, the list: i in int integer is a chain of four words, but the list input integer is not a chain. Note that ever ...
... A list of one or more words is called a chain when each word in that list, except the first, is obtained from the preceding word by appending one or more letters on the right. For instance, the list: i in int integer is a chain of four words, but the list input integer is not a chain. Note that ever ...
1 What is the Subset Sum Problem? 2 An Exact Algorithm for the
... In iteration i, we compute the sums of all subsets of {x1 , x2 , ..., xi }, using as a starting point the sums of all subsets of {x1 , x2 , ..., xi−1 }. Once we find the sum of a subset S’ is greater than t, we ignore that sum, as there is no reason to maintain it. No superset of S’ can possibly be ...
... In iteration i, we compute the sums of all subsets of {x1 , x2 , ..., xi }, using as a starting point the sums of all subsets of {x1 , x2 , ..., xi−1 }. Once we find the sum of a subset S’ is greater than t, we ignore that sum, as there is no reason to maintain it. No superset of S’ can possibly be ...
Algorithms examples Correctness and testing
... • Run your tests by redirecting the standard input and (eventually) the standard output to capture the results. If the input test file is input.txt and the results file is output.txt you can run your program from the ...
... • Run your tests by redirecting the standard input and (eventually) the standard output to capture the results. If the input test file is input.txt and the results file is output.txt you can run your program from the ...
Time Complexity 1
... • Analysis must capture algorithm behavior when problem instances are large – For example, linear search may not be efficient when the list size n = 1,000,000 ...
... • Analysis must capture algorithm behavior when problem instances are large – For example, linear search may not be efficient when the list size n = 1,000,000 ...
Algorithm 1.1 Sequential Search Problem Inputs Outputs
... for (j=0; j < n; j++) { // something of O(1) } // end for ...
... for (j=0; j < n; j++) { // something of O(1) } // end for ...
I p - Jad Matta
... Lemma: A lower bound on the expected number of probes required by any randomized algorithm to solve the Find-bill problem is (n + 1)/2. Proof: We assume that the bill is located in any one of the n boxes uniformly at random. We only consider deterministic algorithms that does not probe the same box ...
... Lemma: A lower bound on the expected number of probes required by any randomized algorithm to solve the Find-bill problem is (n + 1)/2. Proof: We assume that the bill is located in any one of the n boxes uniformly at random. We only consider deterministic algorithms that does not probe the same box ...
Introduction to Randomized Algorithms.
... Application of Yao’s Lemma Lemma: A lower bound on the expected number of probes required by any randomized algorithm to solve the Find-bill problem is (n + 1)/2. Proof: We assume that the bill is located in any one of the n boxes uniformly at random. We only consider deterministic algorithms that ...
... Application of Yao’s Lemma Lemma: A lower bound on the expected number of probes required by any randomized algorithm to solve the Find-bill problem is (n + 1)/2. Proof: We assume that the bill is located in any one of the n boxes uniformly at random. We only consider deterministic algorithms that ...
Project 3 - WCU Computer Science
... For case 3, you need input just one string and then, print a number which represents the number of characters in the string. For case 4, input a string and a position number x which represents the starting position of the sub-string and a position number y which represents the ending position. Print ...
... For case 3, you need input just one string and then, print a number which represents the number of characters in the string. For case 4, input a string and a position number x which represents the starting position of the sub-string and a position number y which represents the ending position. Print ...
Lecture 2 - Rabie A. Ramadan
... If we first multiply the value by 10. We can then store this as an integer between -100 and +100. This needs only 1 byte, a savings of 3 to 7 bytes. A program that stores 1000 of these values can save 3000 to 7000 bytes. It makes a big difference when programming mobile or PDAs or when you have larg ...
... If we first multiply the value by 10. We can then store this as an integer between -100 and +100. This needs only 1 byte, a savings of 3 to 7 bytes. A program that stores 1000 of these values can save 3000 to 7000 bytes. It makes a big difference when programming mobile or PDAs or when you have larg ...
S 2
... is there no improvement? • In practice, we would analyze only when output is small, otherwise the analysis is non-sense consider complexity in the term of the output size M: #outputs We propose O(2l(n+lM)) time algorithm ...
... is there no improvement? • In practice, we would analyze only when output is small, otherwise the analysis is non-sense consider complexity in the term of the output size M: #outputs We propose O(2l(n+lM)) time algorithm ...
ANALYSIS OF ALGORITHMS
... communicate high level ideas and not implementation details (programming language specifics) ...
... communicate high level ideas and not implementation details (programming language specifics) ...
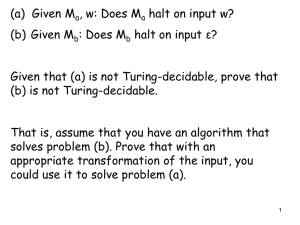
empty-stack
... The following languages are Turingdecidable: (a) {“M” ”w” : M halts on w after at most 700 steps} (b) {“M” “w”: M halts on w without using more than the first 100 tape squares} For part (b): we only have to simulate M for a finite number of steps and in that time frame it will either halt, hang, us ...
... The following languages are Turingdecidable: (a) {“M” ”w” : M halts on w after at most 700 steps} (b) {“M” “w”: M halts on w without using more than the first 100 tape squares} For part (b): we only have to simulate M for a finite number of steps and in that time frame it will either halt, hang, us ...
String-Matching Problem
... The probability of a false positive hit for a random input is 1/q The expected number of false positive hits is O( n/q ) The expected run time of Rabin-Karp is O( n ) + O( m ( v + n/q ))) if v is the number of valid shifts (hits) If we choose q ≥ m and have only a constant number of hits, then ...
... The probability of a false positive hit for a random input is 1/q The expected number of false positive hits is O( n/q ) The expected run time of Rabin-Karp is O( n ) + O( m ( v + n/q ))) if v is the number of valid shifts (hits) If we choose q ≥ m and have only a constant number of hits, then ...
Java Exercises
... a) Read the coefficients a, b, and c of a quadratic equation ax2 + bx + c = 0 as three floating point (number with a decimal point) values from the user. b) Calculate and print a message indicating whether the corresponding equation has one, two or no real roots. Problem 4 (15%) Modify your program ...
... a) Read the coefficients a, b, and c of a quadratic equation ax2 + bx + c = 0 as three floating point (number with a decimal point) values from the user. b) Calculate and print a message indicating whether the corresponding equation has one, two or no real roots. Problem 4 (15%) Modify your program ...
OLD_s1a_alg_analysis..
... (2) Each remaining element is read one by one If smaller than the kth element, then it is ignored Otherwise, it is placed in its correct spot in the array, bumping one element out of the array. ...
... (2) Each remaining element is read one by one If smaller than the kth element, then it is ignored Otherwise, it is placed in its correct spot in the array, bumping one element out of the array. ...
Introduction to Algorithms
... Typical Running Time Functions • N2 (quadratic) – Typical for algorithms that process all pairs of data items (double ...
... Typical Running Time Functions • N2 (quadratic) – Typical for algorithms that process all pairs of data items (double ...
Mouse in a Maze - Bowdoin College
... 2. What variables are needed? 3. What computations are required to achieve the output? 4. Usually, the first steps in your algorithm bring input values to the variables. 5. Usually, the last steps display the output 6. So, the middle steps will do the computation. 7. If the process is to be repeated ...
... 2. What variables are needed? 3. What computations are required to achieve the output? 4. Usually, the first steps in your algorithm bring input values to the variables. 5. Usually, the last steps display the output 6. So, the middle steps will do the computation. 7. If the process is to be repeated ...
Pseudocode Structure Diagrams
... Pseudocode is another method of how an algorithm can be written down. In pseudocode, the steps of the algorithm are written in simple English using some reserved words (key words). Pseudocode is usually used when the algorithm is too cumbersome to be displayed as a flowchart. The following reserved ...
... Pseudocode is another method of how an algorithm can be written down. In pseudocode, the steps of the algorithm are written in simple English using some reserved words (key words). Pseudocode is usually used when the algorithm is too cumbersome to be displayed as a flowchart. The following reserved ...
In not more than 150 words: Define what you understand by the term
... COURSE: ICS 801 REG. NO: P58/76170/2012 NAME: Wycliffe Mutangili M. ...
... COURSE: ICS 801 REG. NO: P58/76170/2012 NAME: Wycliffe Mutangili M. ...
Analysis of Algorithms CS 372 Why Study Algorithms?
... • Necessary in any computer programming problem – Improve algorithm efficiency: run faster, process more data, do something that would otherwise be impossible – Solve problems of significantly large sizes – Technology only improves things by a constant factor ...
... • Necessary in any computer programming problem – Improve algorithm efficiency: run faster, process more data, do something that would otherwise be impossible – Solve problems of significantly large sizes – Technology only improves things by a constant factor ...