Introduction to JSON (JavaScript Object Notation)
... What is JSON-RPC? What is JSON-RPC-Java? • JSON-RPC is a simple remote procedure call protocol similar to XML-RPC although it uses the lightweight JSON format instead of XML • JSON-RPC-Java is a Java implementation of the JSON-RPC protocol ...
... What is JSON-RPC? What is JSON-RPC-Java? • JSON-RPC is a simple remote procedure call protocol similar to XML-RPC although it uses the lightweight JSON format instead of XML • JSON-RPC-Java is a Java implementation of the JSON-RPC protocol ...
Socket Programming
... Programming TCP Client-Server in Java All the classes related to sockets are in the java.net package, so make sure to import that package when you program sockets. All the input/output stream classes are in the java.io package, include this also How to open a socket? If you are programming ...
... Programming TCP Client-Server in Java All the classes related to sockets are in the java.net package, so make sure to import that package when you program sockets. All the input/output stream classes are in the java.io package, include this also How to open a socket? If you are programming ...
Applets in Java
... Applets are written in standard Java Applets are not “complete” applications – they plug into a browser Applets can be assumed to have graphics capability Applets run in a “sandbox” security environment, giving them extremely limited access to the resources of the local machine [usually a good t ...
... Applets are written in standard Java Applets are not “complete” applications – they plug into a browser Applets can be assumed to have graphics capability Applets run in a “sandbox” security environment, giving them extremely limited access to the resources of the local machine [usually a good t ...
Hive Computing - Tribury Media, LLC
... • Application level rollbacks are handled via compensating tasks within the process flow • Only the application developer is aware of how to “undo” any of the atomic actions that have been completed • The Hive’s process flow allows the application developer to catch errors generated by the task and ...
... • Application level rollbacks are handled via compensating tasks within the process flow • Only the application developer is aware of how to “undo” any of the atomic actions that have been completed • The Hive’s process flow allows the application developer to catch errors generated by the task and ...
- SCT Web Site
... often needs to know database schema information, such as table names, column names, and column data types. This information can be used in a follow-on attack. These types of attacks employ techniques that will extract data values from the database. Depending on the type of web application, this info ...
... often needs to know database schema information, such as table names, column names, and column data types. This information can be used in a follow-on attack. These types of attacks employ techniques that will extract data values from the database. Depending on the type of web application, this info ...
System Security - Academic Staff Websites Directory
... often needs to know database schema information, such as table names, column names, and column data types. This information can be used in a follow-on attack. These types of attacks employ techniques that will extract data values from the database. Depending on the type of web application, this info ...
... often needs to know database schema information, such as table names, column names, and column data types. This information can be used in a follow-on attack. These types of attacks employ techniques that will extract data values from the database. Depending on the type of web application, this info ...
JBoss and Aspects for Middlware Components
... Dependency Injection • AOP can be used to specify dependencies upon object declaration, and have those dependencies met upon runtime Advantages: removal of dependency on concrete classes and external configurability e.g. Vendor-specific access methods • Can write a generic application and have ...
... Dependency Injection • AOP can be used to specify dependencies upon object declaration, and have those dependencies met upon runtime Advantages: removal of dependency on concrete classes and external configurability e.g. Vendor-specific access methods • Can write a generic application and have ...
Slides - Gustavus Adolphus College
... For each operation of the service interface we define a class to specify how to handle the returned result of the operation. Class must implement the AsyncCallback interface, which
...
... For each operation of the service interface we define a class to specify how to handle the returned result of the operation. Class must implement the AsyncCallback
ASP.Net
... ASP.Net supports CSS and has a good CSS editor CSS classes and styles can be added to a ASP control by using the CssClass attribute
... ASP.Net supports CSS and has a good CSS editor CSS classes and styles can be added to a ASP control by using the CssClass attribute
Ch. 2a ppt
... Programming languages and almost any form of software system evolve always towards higher levels of abstraction hiding hardware and platform details more powerful primitives and interfaces leaving difficult task to intermediaries (compilers, optimizers, automatic load balancing, automatic data ...
... Programming languages and almost any form of software system evolve always towards higher levels of abstraction hiding hardware and platform details more powerful primitives and interfaces leaving difficult task to intermediaries (compilers, optimizers, automatic load balancing, automatic data ...
ppt - Pacific University
... of computer access are accepted as excuses for late programs; therefore, start work on the programs as soon as they are assigned, don't put them off until the last minute. Further, corruption of programs due to bad disk media is also not accepted as an excuse for late programs; therefore, always kee ...
... of computer access are accepted as excuses for late programs; therefore, start work on the programs as soon as they are assigned, don't put them off until the last minute. Further, corruption of programs due to bad disk media is also not accepted as an excuse for late programs; therefore, always kee ...
client server computing
... • For client server connections that involve many interactions between client and server, certain core information may be transmitted on each call. • This state information could easily be removed from the wire if the server remembered the data between calls from the client. • By maintaining the dat ...
... • For client server connections that involve many interactions between client and server, certain core information may be transmitted on each call. • This state information could easily be removed from the wire if the server remembered the data between calls from the client. • By maintaining the dat ...
Presentation3
... welcomeSocket.accept() read request from connectionSocket write reply to connectionSocket ...
... welcomeSocket.accept() read request from connectionSocket write reply to connectionSocket ...
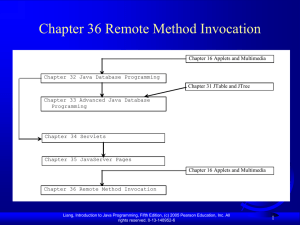
Chapter 18 Networking
... RMI enables you to program at a higher level of abstraction. It hides the details of socket server, socket, connection, and sending or receiving data. It even implements a multithreading server under the hood, whereas with socket-level programming you have to explicitly implement threads for handlin ...
... RMI enables you to program at a higher level of abstraction. It hides the details of socket server, socket, connection, and sending or receiving data. It even implements a multithreading server under the hood, whereas with socket-level programming you have to explicitly implement threads for handlin ...
Objectives
... How does a client locate the remote object? RMI registry provides the registry services for the server to register the object and for the client to locate the object. You can use several overloaded static getRegistry() methods in the LocateRegistry class to return a reference to a Registry. Once a R ...
... How does a client locate the remote object? RMI registry provides the registry services for the server to register the object and for the client to locate the object. You can use several overloaded static getRegistry() methods in the LocateRegistry class to return a reference to a Registry. Once a R ...
Chapter 18 Networking
... RMI enables you to program at a higher level of abstraction. It hides the details of socket server, socket, connection, and sending or receiving data. It even implements a multithreading server under the hood, whereas with socket-level programming you have to explicitly implement threads for handlin ...
... RMI enables you to program at a higher level of abstraction. It hides the details of socket server, socket, connection, and sending or receiving data. It even implements a multithreading server under the hood, whereas with socket-level programming you have to explicitly implement threads for handlin ...
43slide - SIUE Computer Science
... RMI enables you to program at a higher level of abstraction. It hides the details of socket server, socket, connection, and sending or receiving data. It even implements a multithreading server under the hood, whereas with socket-level programming you have to explicitly implement threads for handlin ...
... RMI enables you to program at a higher level of abstraction. It hides the details of socket server, socket, connection, and sending or receiving data. It even implements a multithreading server under the hood, whereas with socket-level programming you have to explicitly implement threads for handlin ...
9. Exceptions
... 9.9. And Finally! … finally try { code that captures a resource } catch (MyException e) { handle e } finally { perhaps dispose of captured resources? } ...
... 9.9. And Finally! … finally try { code that captures a resource } catch (MyException e) { handle e } finally { perhaps dispose of captured resources? } ...
Python Socket Programming
... the Python socket module maps onto the standard C socket library sockets provide a ISO OSI-7 transport level layer interface either UDP or TCP transports can be used both use the Port level of addressing within UDP or TCP ...
... the Python socket module maps onto the standard C socket library sockets provide a ISO OSI-7 transport level layer interface either UDP or TCP transports can be used both use the Port level of addressing within UDP or TCP ...