PPTX - Duke Computer Science
... • Because user code is verified safe, several SIPs can share the same address space. Moreover, SIPS can safely execute at the same privileged level as the kernel. • Eliminating these hardware protection barriers reduces the cost to create and switch contexts between SIPs. • With software isolation, ...
... • Because user code is verified safe, several SIPs can share the same address space. Moreover, SIPS can safely execute at the same privileged level as the kernel. • Eliminating these hardware protection barriers reduces the cost to create and switch contexts between SIPs. • With software isolation, ...
Processes and Threads
... Not just for CPU parallelism: I/O parallelism can be achieved even if I/O operations are “blocking” Program structuring: for example, servers dealing with ...
... Not just for CPU parallelism: I/O parallelism can be achieved even if I/O operations are “blocking” Program structuring: for example, servers dealing with ...
ppt
... SPIN is a dynamically extensible operating system that allows user applications to safely change the operating system's interface and implementation. Extensions are linked into the operating system kernel at application runtime, enabling them to access system services with low overhead. ...
... SPIN is a dynamically extensible operating system that allows user applications to safely change the operating system's interface and implementation. Extensions are linked into the operating system kernel at application runtime, enabling them to access system services with low overhead. ...
PPTX - Duke Computer Science
... Microkernel operating systems, such as Mach [1], L4 [24], SPIN [6], VINO [38], Taos/Topaz [45], and the Exokernel [11], partition the components of a monolithic operating system kernel into separate processes to increase the system’s failure isolation and reduce development complexity. The sealed pr ...
... Microkernel operating systems, such as Mach [1], L4 [24], SPIN [6], VINO [38], Taos/Topaz [45], and the Exokernel [11], partition the components of a monolithic operating system kernel into separate processes to increase the system’s failure isolation and reduce development complexity. The sealed pr ...
Unit-5 - Ipemgzb.ac.in
... The job of allocating CPU time to different tasks within an operating system. While scheduling is normally thought of as the running and interrupting of processes, in Linux, scheduling also includes the running of the various kernel tasks. Running kernel tasks encompasses both tasks that are request ...
... The job of allocating CPU time to different tasks within an operating system. While scheduling is normally thought of as the running and interrupting of processes, in Linux, scheduling also includes the running of the various kernel tasks. Running kernel tasks encompasses both tasks that are request ...
PPT - Defcon
... • Overwrite the first seven bytes of SwapContext with a jump to our Detour function • The EDI register points to the KTHREAD of the thread to be scheduled to run • Our Detour function follows the KTHREAD to the EPROCESS block and determines if it is still appropriately linked in the list of active p ...
... • Overwrite the first seven bytes of SwapContext with a jump to our Detour function • The EDI register points to the KTHREAD of the thread to be scheduled to run • Our Detour function follows the KTHREAD to the EPROCESS block and determines if it is still appropriately linked in the list of active p ...
Operating System Concepts for System Programmers
... is called booting process. Following are the various steps involved while booting the OS: The BIOS program present in the non-volatile (ROM/Flash) memory of a computer will run first. In fact whenever a CPU is powered on, it tries to fetch (read) instructions from a fixed start address. The computer ...
... is called booting process. Following are the various steps involved while booting the OS: The BIOS program present in the non-volatile (ROM/Flash) memory of a computer will run first. In fact whenever a CPU is powered on, it tries to fetch (read) instructions from a fixed start address. The computer ...
Processes and System Calls
... How does the kernel know which system call the application is requesting? • A. system call codes – the kernel defines a code for each system call it understands – the kernel expects the application to place a code in a specified location before executing the syscall instruction ∗ for OS/161 on the M ...
... How does the kernel know which system call the application is requesting? • A. system call codes – the kernel defines a code for each system call it understands – the kernel expects the application to place a code in a specified location before executing the syscall instruction ∗ for OS/161 on the M ...
Processes and System Calls
... How does the kernel know which system call the application is requesting? • A. system call codes – the kernel defines a code for each system call it understands – the kernel expects the application to place a code in a specified location before executing the syscall instruction ∗ for OS/161 on the M ...
... How does the kernel know which system call the application is requesting? • A. system call codes – the kernel defines a code for each system call it understands – the kernel expects the application to place a code in a specified location before executing the syscall instruction ∗ for OS/161 on the M ...
2. Operating System Models
... Todays operating systems provide two fundamental services for users. First, they make the computer hardware easier to use. They create a virtual machine that differs markedly from the real machine. Indeed, the computer revolution of the last two decades is due, in part, to the success that operatin ...
... Todays operating systems provide two fundamental services for users. First, they make the computer hardware easier to use. They create a virtual machine that differs markedly from the real machine. Indeed, the computer revolution of the last two decades is due, in part, to the success that operatin ...
Kernel
... – memory resident part of UNIX – majority written in C rest in assembler language (HW dependent, speed) – a.out (a plain C a.out program) – consists of functions • other programs can call (some of) these functions • called “system call function” ...
... – memory resident part of UNIX – majority written in C rest in assembler language (HW dependent, speed) – a.out (a plain C a.out program) – consists of functions • other programs can call (some of) these functions • called “system call function” ...
PowerPoint 簡報
... The high-level networking code is here (e.g. socket.c). The low-level network drivers pass received packets up to and get packets to send from this level, which may pass the data to a user-level application, discard the data, or use it in-kernel, depending on the packet. • The net/core directory con ...
... The high-level networking code is here (e.g. socket.c). The low-level network drivers pass received packets up to and get packets to send from this level, which may pass the data to a user-level application, discard the data, or use it in-kernel, depending on the packet. • The net/core directory con ...
operation
... • Therefore the sizes of kernels differ widely. • Mach (OSF-1) uses several MByte memory footprint, while Cosy (own development) only needs some 100KB. ...
... • Therefore the sizes of kernels differ widely. • Mach (OSF-1) uses several MByte memory footprint, while Cosy (own development) only needs some 100KB. ...
PowerPoint
... “The basic object-reference mechanism in Mach and is implemented as a kernel-protected communication channel. Communication is accomplished by sending messages to ports; messages are queued at the destination port if no thread is immediately ready to receive them. Ports are protected by kernel-man ...
... “The basic object-reference mechanism in Mach and is implemented as a kernel-protected communication channel. Communication is accomplished by sending messages to ports; messages are queued at the destination port if no thread is immediately ready to receive them. Ports are protected by kernel-man ...
Operating System Kernel More Virtual Stuff
... Goal: create illusion of large virtual address space • divide address into (VPN,offset), map to (PPN,offset) or page fault • use high address bits to select page: keep related data on same page • use cache (TLB) to speed up mapping mechanism—works well • long disk latencies: keep working set in phys ...
... Goal: create illusion of large virtual address space • divide address into (VPN,offset), map to (PPN,offset) or page fault • use high address bits to select page: keep related data on same page • use cache (TLB) to speed up mapping mechanism—works well • long disk latencies: keep working set in phys ...
PPT - UNL CSE
... Tom is deploying a new server program for his client. During the field test, he notices that its performance is below his expectation. How would he identify the main causes? A company is planning to upgrade the server systems. You are asked to analyze which systems and which configurations will ...
... Tom is deploying a new server program for his client. During the field test, he notices that its performance is below his expectation. How would he identify the main causes? A company is planning to upgrade the server systems. You are asked to analyze which systems and which configurations will ...
ppt
... "responsibility" of the kernel, and most things are done in userspace with communication via IPC. But doesn't this use of IPC impose a dramatic speed-hit? How fast is the Mach system? It seems that all this flexibility and simplicity through use of simple primitives will come at a large overhead. ...
... "responsibility" of the kernel, and most things are done in userspace with communication via IPC. But doesn't this use of IPC impose a dramatic speed-hit? How fast is the Mach system? It seems that all this flexibility and simplicity through use of simple primitives will come at a large overhead. ...
ing systems were being developed in the
... The reasons that such a modular, multiserver design is better than a monolithic one are threefold. First, by moving most of the code from kernel mode to user mode, we are not reducing the number of bugs but we are reducing the power of each bug to cause damage. Bugs in user-mode processes have much ...
... The reasons that such a modular, multiserver design is better than a monolithic one are threefold. First, by moving most of the code from kernel mode to user mode, we are not reducing the number of bugs but we are reducing the power of each bug to cause damage. Bugs in user-mode processes have much ...
Kernel (computer science)
... allow programs to use more memory than the system has physically available. When a program needs data which is not currently in RAM, the CPU signals to the kernel that this has happened, and the kernel responds by writing the contents of an inactive memory block to disk (if necessary) and replacing ...
... allow programs to use more memory than the system has physically available. When a program needs data which is not currently in RAM, the CPU signals to the kernel that this has happened, and the kernel responds by writing the contents of an inactive memory block to disk (if necessary) and replacing ...
presentation source
... • JRes [Czajkowski ‘98] – instrument bytecode – use callbacks when resource limits have been exceeded ...
... • JRes [Czajkowski ‘98] – instrument bytecode – use callbacks when resource limits have been exceeded ...
slides - Computer Science
... Enables wimp applications to obtain isolated I/O channels to any subset of a system’s commodity devices needed during a session Enables trusted audit and control of physical devices without stopping and restarting applications, Allows unmodified commodity OSes to have unfettered access to all hardwar ...
... Enables wimp applications to obtain isolated I/O channels to any subset of a system’s commodity devices needed during a session Enables trusted audit and control of physical devices without stopping and restarting applications, Allows unmodified commodity OSes to have unfettered access to all hardwar ...
ppt
... Physical address service : controls the use and allocation of physical pages. Virtual address service: Allocates capabilities for virtual addresses Translation service: Express the relationship between virtual addresses and physical memory • Support services like demand-paging, copy-onwrite, d ...
... Physical address service : controls the use and allocation of physical pages. Virtual address service: Allocates capabilities for virtual addresses Translation service: Express the relationship between virtual addresses and physical memory • Support services like demand-paging, copy-onwrite, d ...
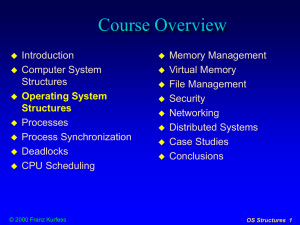
Operating System Structures
... operating system provides services and manages resources user processes request services from the OS through system calls ...
... operating system provides services and manages resources user processes request services from the OS through system calls ...
The Architecture of a Reliable Operating System,
... microkernel approach. The combination of legacy applications and real-time or secure modules allows for a smooth transition to a new computing environment. Mach-UX [1] was one of the first systems to run BSD UNIX in user-mode on top of the Mach 3 microkernel, as shown in Fig. 2(a). Another example, ...
... microkernel approach. The combination of legacy applications and real-time or secure modules allows for a smooth transition to a new computing environment. Mach-UX [1] was one of the first systems to run BSD UNIX in user-mode on top of the Mach 3 microkernel, as shown in Fig. 2(a). Another example, ...
ppt
... A grouping of ports in the same task Used for using a single thread as an incoming queue processor (e.g. Unix select or poll system calls) A port may be a member of one set at a time ...
... A grouping of ports in the same task Used for using a single thread as an incoming queue processor (e.g. Unix select or poll system calls) A port may be a member of one set at a time ...
Kernel (operating system)
In computing, the kernel is a computer program that manages I/O requests from software, and translates them into data processing instructions for the central processing unit and other electronic components of a computer. The kernel is a fundamental part of a modern computer's operating system.The critical code of the kernel is usually loaded into a protected area of memory, which prevents it from being overwritten by other, less frequently used parts of the operating system or by applications. The kernel performs its tasks, such as executing processes and handling interrupts, in kernel space, whereas everything a user normally does, such as writing text in a text editor or running programs in a GUI (graphical user interface), is done in user space. This separation prevents user data and kernel data from interfering with each other and thereby diminishing performance or causing the system to become unstable (and possibly crashing). When a process makes requests of the kernel, the request is called a system call. Various kernel designs differ in how they manage system calls and resources. For example, a monolithic kernel executes all the operating system instructions in the same address space in order to improve the performance of the system. A microkernel runs most of the operating system's background processes in user space, to make the operating system more modular and, therefore, easier to maintain.The kernel's interface is a low-level abstraction layer.