E - Read
... Let Xi;j be the subset of X such that RandQS(Xi;j ) is the ¯rst subroutine call such that its x belongs to the set fxi ; xi+1 ; : : : ; xj g. Clearly, fxi ; : : : ; xj g µ Xi;j . This speci¯c choice of x determines whether xi and xj will ever be compared to each other throughout the execution In par ...
... Let Xi;j be the subset of X such that RandQS(Xi;j ) is the ¯rst subroutine call such that its x belongs to the set fxi ; xi+1 ; : : : ; xj g. Clearly, fxi ; : : : ; xj g µ Xi;j . This speci¯c choice of x determines whether xi and xj will ever be compared to each other throughout the execution In par ...
154 kb - Mahopac Central School District
... descriptions of objects and events and to from their own tentative explanations of what they have observed. Key Idea 2: Beyond the use of reasoning & consensus, scientific inquiry involves the testing of proposed explanations involving the use of conventional techniques & procedures & usually requir ...
... descriptions of objects and events and to from their own tentative explanations of what they have observed. Key Idea 2: Beyond the use of reasoning & consensus, scientific inquiry involves the testing of proposed explanations involving the use of conventional techniques & procedures & usually requir ...
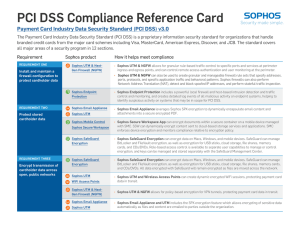
PCI DSS Compliance Reference Card
... The Payment Card Industry Data Security Standard (PCI DSS) is a proprietary information security standard for organizations that handle branded credit cards from the major card schemes including Visa, MasterCard, American Express, Discover, and JCB. The standard covers all major areas of a security ...
... The Payment Card Industry Data Security Standard (PCI DSS) is a proprietary information security standard for organizations that handle branded credit cards from the major card schemes including Visa, MasterCard, American Express, Discover, and JCB. The standard covers all major areas of a security ...
Paper ~ Which Algorithm Should I Choose At Any Point of the
... run for quite some time. If it is a very good algorithm that excels in small, medium and large budgets, then only it will run from then on. However, if it is an algorithm that converges fast to a local optimum, as discussed above, then it will run for awhile and gradually the predicted performance w ...
... run for quite some time. If it is a very good algorithm that excels in small, medium and large budgets, then only it will run from then on. However, if it is an algorithm that converges fast to a local optimum, as discussed above, then it will run for awhile and gradually the predicted performance w ...
EE579T-Class 4
... The computer can factor any N, using the trial division method, in approximately N0.5/1010 seconds. If N has 100 digits, this process will require approximately ...
... The computer can factor any N, using the trial division method, in approximately N0.5/1010 seconds. If N has 100 digits, this process will require approximately ...
SecuROM™ Disc Check
... SecuROM™ is the only digital rights management solution that effectively combats all three major piracy threats: digital clones, emulation, and cracks. Digital Clones are discs that are copied onto CD-R, DVD-R or hard disk. Also known as 1:1, friend-to-friend, or casual copies, digital cloning is th ...
... SecuROM™ is the only digital rights management solution that effectively combats all three major piracy threats: digital clones, emulation, and cracks. Digital Clones are discs that are copied onto CD-R, DVD-R or hard disk. Also known as 1:1, friend-to-friend, or casual copies, digital cloning is th ...
FinalNailWEP
... What is WEP (Wired Equivalent Privacy)? WEP uses a RC4 cipher (stream cipher) which attempts to keep the wireless data private and exact. WEP is broken (well-known fact) However, few people are capable of carrying out an attack ...
... What is WEP (Wired Equivalent Privacy)? WEP uses a RC4 cipher (stream cipher) which attempts to keep the wireless data private and exact. WEP is broken (well-known fact) However, few people are capable of carrying out an attack ...
2×2 handouts
... be much time consuming task. That is why mostly so called ”standard or ”named’ elliptic curves are used that have been published by some standardization bodies. ...
... be much time consuming task. That is why mostly so called ”standard or ”named’ elliptic curves are used that have been published by some standardization bodies. ...
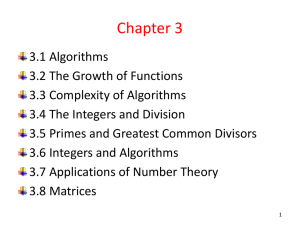
A+B
... • We say that f(x) is Ω(g(x)) if there are positive constants C and k such that |f(x)|≥ C|g(x)| Whenever x > k. ( this is read as “f(x) is big-Omega of g(x)” .) • Example 10 :The function f(x) =8x3+ 5x2 +7 is Ω(g(x)) , where g(x) is the function g(x) =x3. • This is easy to see because f(x) =8x3+ 5x2 ...
... • We say that f(x) is Ω(g(x)) if there are positive constants C and k such that |f(x)|≥ C|g(x)| Whenever x > k. ( this is read as “f(x) is big-Omega of g(x)” .) • Example 10 :The function f(x) =8x3+ 5x2 +7 is Ω(g(x)) , where g(x) is the function g(x) =x3. • This is easy to see because f(x) =8x3+ 5x2 ...
SNMP
... Provides connection security with two basic properties: 1. Connection privacy. Symmetric cryptography is used for data encryption (e.g. DES, 3DES,RC4). Encryption can be turned off. 2. The connection is securely reliable. Message transport includes a keyed cryptographic message authentication check ...
... Provides connection security with two basic properties: 1. Connection privacy. Symmetric cryptography is used for data encryption (e.g. DES, 3DES,RC4). Encryption can be turned off. 2. The connection is securely reliable. Message transport includes a keyed cryptographic message authentication check ...
Part VIII Elliptic curves cryptography and factorization
... Let us continue to discuss the following key problem for factorization using elliptic curves: Problem: How to choose k such that for a given point P we should try to compute points iP or 2i P for all multiples of P smaller than kP? Idea: If one searches for m-digits factors, one chooses k in such a ...
... Let us continue to discuss the following key problem for factorization using elliptic curves: Problem: How to choose k such that for a given point P we should try to compute points iP or 2i P for all multiples of P smaller than kP? Idea: If one searches for m-digits factors, one chooses k in such a ...
4. Preliminary remarks on Algebraic Groups
... This book is now completed and an edited version of it will be published by Cambridge University Press in early 2012. Some of the Theorem/Lemma/Exercise numbers may be different in the published version. Please send an email to [email protected] if you find any mistakes. All feedback o ...
... This book is now completed and an edited version of it will be published by Cambridge University Press in early 2012. Some of the Theorem/Lemma/Exercise numbers may be different in the published version. Please send an email to [email protected] if you find any mistakes. All feedback o ...
doc.gold.ac.uk
... • Today’s computing – Requires comprehensive computer security plans Electronic Commerce, Tenth Edition ...
... • Today’s computing – Requires comprehensive computer security plans Electronic Commerce, Tenth Edition ...
Certified Penetration Testing Specialist
... vulnerability consultants. Mile2 trainers keep abreast of their expertise by practicing what they teach because we believe that an equal emphasis on theoretical and real world experience is essential for effective knowledge transfer to you, the student. The CPTS presents information on the latest vu ...
... vulnerability consultants. Mile2 trainers keep abreast of their expertise by practicing what they teach because we believe that an equal emphasis on theoretical and real world experience is essential for effective knowledge transfer to you, the student. The CPTS presents information on the latest vu ...
4-RSA
... encryption exponent e is not protected by RSA. Say, e 3, and Bob sends a message m to three recipients encrypted as: c1 m3 mod n1, c 2 m3 mod n2 , c3 m3 mod n3. Eve intercepts the three ciphertexts, and recovers m: m3 c1 mod n1 , m3 c2 mod n2 , m3 c 3 mod n3. By CRT, m3 c mod n1n ...
... encryption exponent e is not protected by RSA. Say, e 3, and Bob sends a message m to three recipients encrypted as: c1 m3 mod n1, c 2 m3 mod n2 , c3 m3 mod n3. Eve intercepts the three ciphertexts, and recovers m: m3 c1 mod n1 , m3 c2 mod n2 , m3 c 3 mod n3. By CRT, m3 c mod n1n ...
Statistical Models for Steganography - uni
... Binary partition (C0, C1) of the set C of possible cover texts Alice is active if and only if the observed message ‘c’ is contained in C1. Type II error Eve fails to detect ...
... Binary partition (C0, C1) of the set C of possible cover texts Alice is active if and only if the observed message ‘c’ is contained in C1. Type II error Eve fails to detect ...
SSH - Information Services and Technology
... analysis is usually performed by other security applications on a system. ...
... analysis is usually performed by other security applications on a system. ...
Application Security within Java 2, Standard Edition (J2SE)
... In order to perform JAAS authorization, you need to know three things. You need to know 1) who or what is authorizing, 2) the resource they are trying to use and 3) what they are actually trying to do with the resource (read, write, execute, ...
... In order to perform JAAS authorization, you need to know three things. You need to know 1) who or what is authorizing, 2) the resource they are trying to use and 3) what they are actually trying to do with the resource (read, write, execute, ...
離散對數密碼系統 - 國立交通大學資訊工程學系NCTU Department of
... Discrete Logarithm Problem • Let G is a finite cyclic group of size n generated by generator g, i.e. G = = {g i | i = 1, 2, …, n}
or {g i | i = 0, 1, …, n-1}
– Given g and i, it is easy to compute gi by repeated squaring
– Discrete logarithm problem
x
Given a G , find x such that g a
We den ...
... Discrete Logarithm Problem • Let G is a finite cyclic group of size n generated by generator g, i.e. G =
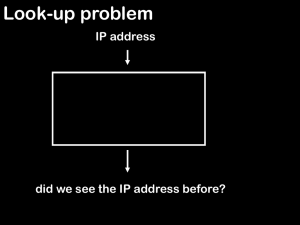
Hashing
... Perfect hashing Goal: worst-case O(1) search space used O(m) static set of elements n = m2 ...
... Perfect hashing Goal: worst-case O(1) search space used O(m) static set of elements n = m2 ...
Protecting the FPGA Design From Common Threats
... Though the definition of zeroization involves a clear plus verification that all data was cleared, most applications will benefit from a zeroization which clears all memory cells of the FPGA. The Cyclone III LS zeroization solution breaks out the clear function and the verification function to provi ...
... Though the definition of zeroization involves a clear plus verification that all data was cleared, most applications will benefit from a zeroization which clears all memory cells of the FPGA. The Cyclone III LS zeroization solution breaks out the clear function and the verification function to provi ...
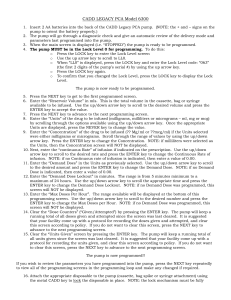
CADD LEGACY PCA Model 6300
... o Enter the Clinician Bolus Code “997” by pressing the N arrow key three times to count backwards from 999. o Press the LOCK key again. o Enter the amount of drug to be infused using the Y arrow key. The allowable range will be displayed at the bottom of this screen. o Press the ENTER key to adminis ...
... o Enter the Clinician Bolus Code “997” by pressing the N arrow key three times to count backwards from 999. o Press the LOCK key again. o Enter the amount of drug to be infused using the Y arrow key. The allowable range will be displayed at the bottom of this screen. o Press the ENTER key to adminis ...
Cryptography

Cryptography or cryptology; from Greek κρυπτός kryptós, ""hidden, secret""; and γράφειν graphein, ""writing"", or -λογία -logia, ""study"", respectively is the practice and study of techniques for secure communication in the presence of third parties (called adversaries). More generally, it is about constructing and analyzing protocols that block adversaries; various aspects in information security such as data confidentiality, data integrity, authentication, and non-repudiation are central to modern cryptography. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, and electrical engineering. Applications of cryptography include ATM cards, computer passwords, and electronic commerce.Cryptography prior to the modern age was effectively synonymous with encryption, the conversion of information from a readable state to apparent nonsense. The originator of an encrypted message shared the decoding technique needed to recover the original information only with intended recipients, thereby precluding unwanted persons from doing the same. Since World War I and the advent of the computer, the methods used to carry out cryptology have become increasingly complex and its application more widespread.Modern cryptography is heavily based on mathematical theory and computer science practice; cryptographic algorithms are designed around computational hardness assumptions, making such algorithms hard to break in practice by any adversary. It is theoretically possible to break such a system, but it is infeasible to do so by any known practical means. These schemes are therefore termed computationally secure; theoretical advances, e.g., improvements in integer factorization algorithms, and faster computing technology require these solutions to be continually adapted. There exist information-theoretically secure schemes that provably cannot be broken even with unlimited computing power—an example is the one-time pad—but these schemes are more difficult to implement than the best theoretically breakable but computationally secure mechanisms.The growth of cryptographic technology has raised a number of legal issues in the information age. Cryptography's potential for use as a tool for espionage and sedition has led many governments to classify it as a weapon and to limit or even prohibit its use and export. In some jurisdictions where the use of cryptography is legal, laws permit investigators to compel the disclosure of encryption keys for documents relevant to an investigation. Cryptography also plays a major role in digital rights management and piracy of digital media.