Identification and Recognition of Remote
... of the most prolific kinds of malicious software. Although numbers vary, in extreme cases such as Conficker, Bredolab and Mariposa, one botnet can span up to several million infected computers. This way, attackers draw substantial revenue by monetizing their bot-infected computers. This thesis encap ...
... of the most prolific kinds of malicious software. Although numbers vary, in extreme cases such as Conficker, Bredolab and Mariposa, one botnet can span up to several million infected computers. This way, attackers draw substantial revenue by monetizing their bot-infected computers. This thesis encap ...
doc - John L. Pollock
... We can think of these considerations as giving us a reason for believing that (under the present circumstances) the object’s looking red does not guarantee that it is red. It will be convenient to symbolize this as “(x looks red) (x is red)”. As was just illustrated, we can discover new probabilis ...
... We can think of these considerations as giving us a reason for believing that (under the present circumstances) the object’s looking red does not guarantee that it is red. It will be convenient to symbolize this as “(x looks red) (x is red)”. As was just illustrated, we can discover new probabilis ...
An analytic approach for obtaining maximal entropy OWA operator weights ∗ Robert Full´er
... Additionally, Fuller and Majlender (2001) used Lagrange multipliers on Yager’s OWA equation to derive a polynomial equation, which determines the optimal weighting vector under maximal entropy (ME-OWA operator). The proposed approach thus determines the optimal weighting vector under maximal entropy ...
... Additionally, Fuller and Majlender (2001) used Lagrange multipliers on Yager’s OWA equation to derive a polynomial equation, which determines the optimal weighting vector under maximal entropy (ME-OWA operator). The proposed approach thus determines the optimal weighting vector under maximal entropy ...
Redalyc.Rational versus Intuitive Outcomes of Reasoning with
... of Cheesecake. You want to get as many cakes as possible, and the following are the rules of the game. a) You can take cakes from the table in two ’rounds’: 1. In the first round you can take at most two cakes; 2. In the second round you can take at most one cake. b) If you take Almond cake and Chee ...
... of Cheesecake. You want to get as many cakes as possible, and the following are the rules of the game. a) You can take cakes from the table in two ’rounds’: 1. In the first round you can take at most two cakes; 2. In the second round you can take at most one cake. b) If you take Almond cake and Chee ...
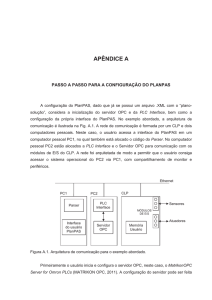
apêndice a - Repositório Institucional
... neural network whose goal was to simulate the human brain in computational operations. Since then, there were developed many tools related with artificial intelligence, such as expert systems, neural networks, genetic algorithms, fuzzy logic and especially, automated planners, however, it has not be ...
... neural network whose goal was to simulate the human brain in computational operations. Since then, there were developed many tools related with artificial intelligence, such as expert systems, neural networks, genetic algorithms, fuzzy logic and especially, automated planners, however, it has not be ...
Software Performance Estimation Methods for System
... source code, called intermediate source code (ISC), which has a structure close to the structure of its binary code and thus allows for accurate back-annotation of the timing information obtained from the binary level. The back-annotated timing information can also be aggregated correctly along the ...
... source code, called intermediate source code (ISC), which has a structure close to the structure of its binary code and thus allows for accurate back-annotation of the timing information obtained from the binary level. The back-annotated timing information can also be aggregated correctly along the ...
Intelligence by Design - Department of Computer Science
... action. Search is only likely to succeed in resource-bounded agents if they have already been biased towards finding the right answer. In artificial agents, the primary source of bias is engineering. This dissertation describes an approach, Behavior-Oriented Design (BOD) for engineering complex agen ...
... action. Search is only likely to succeed in resource-bounded agents if they have already been biased towards finding the right answer. In artificial agents, the primary source of bias is engineering. This dissertation describes an approach, Behavior-Oriented Design (BOD) for engineering complex agen ...
Publication : An introduction to Soar as an agent architecture
... PSCM, knowing that some operation can be applied in some situation is distinct from knowing how to execute that operation, or if it is likely to result in progress within the problem space. The knowledge representations of Soar reflect this distinction by requiring independent representations of the ...
... PSCM, knowing that some operation can be applied in some situation is distinct from knowing how to execute that operation, or if it is likely to result in progress within the problem space. The knowledge representations of Soar reflect this distinction by requiring independent representations of the ...
implementing a decision support system for online job seeking
... solution consistent with a series of constraints. Suggestion models that perform the logical processing leading to a specific suggested decision for a fairly structured or well-understood task. Donovan and Madnick (1977) classified DSS as institutional or ad hoc. Institutional DSS support decisions ...
... solution consistent with a series of constraints. Suggestion models that perform the logical processing leading to a specific suggested decision for a fairly structured or well-understood task. Donovan and Madnick (1977) classified DSS as institutional or ad hoc. Institutional DSS support decisions ...
Cardoso, A., Veale, T., Wiggins, G.
... Creativity is an elusive phenomenon to study, or even to define, made all the more vexing by our fundamental inability to pin it down in formal terms. Ask most people the question “what is creativity?” and you are more likely to elicit an anecdote, an aphorism, or a metaphor, than you are a literal ...
... Creativity is an elusive phenomenon to study, or even to define, made all the more vexing by our fundamental inability to pin it down in formal terms. Ask most people the question “what is creativity?” and you are more likely to elicit an anecdote, an aphorism, or a metaphor, than you are a literal ...
Survey on Fuzzy Expert System
... sorted neighborhood method (SNM) in which key is created for each tuples such that the duplicates will have similar keys. The tuples are sorted using the key and finally a window of size w slides over the sorted data and performing n (w-1) comparison where n is total no of tuples after comparison th ...
... sorted neighborhood method (SNM) in which key is created for each tuples such that the duplicates will have similar keys. The tuples are sorted using the key and finally a window of size w slides over the sorted data and performing n (w-1) comparison where n is total no of tuples after comparison th ...
Intelligent Agents - Department of Computer Science, Oxford
... intelligent agent is one that is capable of flexible autonomous action in order to meet its design objectives, where by flexible, I mean three things [71]: reactivity: intelligent agents are able to perceive their environment, and respond in a timely fashion to changes that occur in it in order to s ...
... intelligent agent is one that is capable of flexible autonomous action in order to meet its design objectives, where by flexible, I mean three things [71]: reactivity: intelligent agents are able to perceive their environment, and respond in a timely fashion to changes that occur in it in order to s ...
Chapter 02 Decisions and Processes: Value Driven Business
... A. Key performance indicators can have no more than four critical success factors B. Critical success factors can have no more than four key performance indicators C. Key performance indicators can have several critical success factors D. Critical success factors can have several key performance ind ...
... A. Key performance indicators can have no more than four critical success factors B. Critical success factors can have no more than four key performance indicators C. Key performance indicators can have several critical success factors D. Critical success factors can have several key performance ind ...
BCA-601
... the intelligence of computer systems 'Computer applications software engineers' analyze users' needs and design, construct, and maintain specialized utility programs. Software engineers coordinate the construction and maintenance of a company's computer systems and plan their future growth. Software ...
... the intelligence of computer systems 'Computer applications software engineers' analyze users' needs and design, construct, and maintain specialized utility programs. Software engineers coordinate the construction and maintenance of a company's computer systems and plan their future growth. Software ...
D-Link DSL-2760U USER’S MANUAL 1
... DHCP Support – Dynamic Host Configuration Protocol automatically and dynamically assigns all LAN IP settings to each host on your network. This eliminates the need to reconfigure every host whenever changes in network topology occur. Network Address Translation (NAT) – For small office environments, ...
... DHCP Support – Dynamic Host Configuration Protocol automatically and dynamically assigns all LAN IP settings to each host on your network. This eliminates the need to reconfigure every host whenever changes in network topology occur. Network Address Translation (NAT) – For small office environments, ...
D22.1 Analysis of intangible asset management in
... service system modelling had to be introduced, called Model Driven Service Engineering Architecture (MSDEA) that is operating on three levels (strategic, tactical and operational). The MSDEA model, at the strategic or at the so called Business Service Model level, had been proposed to be applied to ...
... service system modelling had to be introduced, called Model Driven Service Engineering Architecture (MSDEA) that is operating on three levels (strategic, tactical and operational). The MSDEA model, at the strategic or at the so called Business Service Model level, had been proposed to be applied to ...